Reliable DOP-C02 Test Tutorial & DOP-C02 Valid Test Voucher - New DOP-C02 Exam Papers - Insideopenoffice
DOP-C02 ' marker.
Also when enabling AAA:
R1#sh run | sec aaa
aaa new-model
aaa authentication login default local
aaa session-id common
NEW QUESTION: 2
An administrator needs to connect a router in one building to a router in another using Ethernet. Each router is connected to a managed switch and the switches are connected to each other via a fiber line. Which of the following should be configured to prevent unauthorized devices from connecting to the network?
A. Configure only one of the routers to run DHCP services
B. Implement port security on the switches
C. Configure each port on the switches to use the same VLAN other than the default one
D. Enable VTP on both switches and set to the same domain
Answer: B
Explanation:
Port security in IT can mean several things:
The physical control of all connection points, such as RJ-45 wall jacks or device ports, so that no unauthorized users or unauthorized devices can attempt to connect into an open port.
The management of TCP and User Datagram Protocol (UDP) ports. If a service is active and assigned to a port, then that port is open. All the other 65,535 ports (of TCP or UDP) are closed if a service isn't actively using them.
Port knocking is a security system in which all ports on a system appear closed. However, if the client sends packets to a specific set of ports in a certain order, a bit like a secret knock, then the desired service port becomes open and allows the client software to connect to the service.
Incorrect Answers:
A. A basic switch not configured for VLANs has VLAN functionality disabled or permanently enabled with a default
VLAN that contains all ports on the device as members. Every device connected to one of its ports can send packets to any of the others. Separating ports by VLAN groups separates their traffic very much like connecting the devices to another, distinct switch of their own. Configuration of the first custom VLAN port group usually involves removing ports from the default VLAN, such that the first custom group of VLAN ports is actually the second VLAN on the device, in addition to the default VLAN
B. VLAN Trunking Protocol (VTP) is a Cisco proprietary protocol that broadcasts the definition of Virtual Local Area
Networks (VLAN) on the whole local area network. VTP achieves this by carrying VLAN information to all the switches in a VTP domain.
C. The Dynamic Host Configuration Protocol (DHCP) is a standardized network protocol used on Internet Protocol (IP) networks for dynamically distributing network configuration parameters, such as IP addresses for interfaces and services.
References:
Stewart, James Michael, CompTIA Security+ Review Guide, Sybex, Indianapolis, 2014, p. 24
http://en.wikipedia.org/wiki/VLAN_Trunking_Protocol
http://en.wikipedia.org/wiki/Dynamic_Host_Configuration_Protocol
http://en.wikipedia.org/wiki/Virtual_LAN
NEW QUESTION: 3
SysOps管理者は、セキュリティのベストプラクティスがAWSアカウントのrootユーザーで実行されていることを確認する必要があります。
これが行われたことを管理者はどのように確認する必要がありますか?
A. ルートユーザーの構成を管理するAWS ArtifactからAWSコンプライアンスドキュメントを定期的に配布します。
B. AWS CLIを定期的に使用して、rootユーザーのパスワードを変更します。
C. AWS CLIを定期的に使用して、rootユーザーのアクセスキーとシークレットキーをローテーションします。
D. AWS Trusted Advisorのセキュリティチェックを使用して、ルートユーザーの構成を確認します。
Answer: D
- B2C-Commerce-Architect Online Tests
- Answers Arch-303 Free
- DP-420 Latest Real Exam
- Valid Braindumps HPE3-CL09 Ppt
- Reliable TDA-C01 Test Cost
- Test 156-560 Cram
- New AP-215 Test Discount
- 300-640 Reliable Test Test
- 72201T Valid Test Sims
- HPE7-M02 Reliable Test Vce
- C-BCBAI-2601 Test Questions Answers
- CAP-2101-20 Test Testking
- Test NCA-GENM Guide
- H19-132_V1.0 Test Valid
- HPE3-CL09 Exam Vce Free
- MB-240 Test Registration
- 1D0-1057-25-D Certification Torrent
- C-TS4FI-2023 New Practice Materials
- Pass Leader JN0-232 Dumps
- Clearer NCA-AIIO Explanation
- CISM Test Dates
- XK0-006 Knowledge Points
- Valid RCWA Learning Materials
| Questions and Answers | : 347 |
| File Format | |
| Windows Compatibility | : Windows 10/8/7/Vista/2000/XP/98 |
| Mac Compatibility | : All Versions including iOS 4/5/6/7 |
| Android | : All Android Versions |
| Linux | : All Linux Versions |
Also when enabling AAA:
R1#sh run | sec aaa
aaa new-model
aaa authentication login default local
aaa session-id common
NEW QUESTION: 2
An administrator needs to connect a router in one building to a router in another using Ethernet. Each router is connected to a managed switch and the switches are connected to each other via a fiber line. Which of the following should be configured to prevent unauthorized devices from connecting to the network?
A. Configure only one of the routers to run DHCP services
B. Implement port security on the switches
C. Configure each port on the switches to use the same VLAN other than the default one
D. Enable VTP on both switches and set to the same domain
Answer: B
Explanation:
Port security in IT can mean several things:
The physical control of all connection points, such as RJ-45 wall jacks or device ports, so that no unauthorized users or unauthorized devices can attempt to connect into an open port.
The management of TCP and User Datagram Protocol (UDP) ports. If a service is active and assigned to a port, then that port is open. All the other 65,535 ports (of TCP or UDP) are closed if a service isn't actively using them.
Port knocking is a security system in which all ports on a system appear closed. However, if the client sends packets to a specific set of ports in a certain order, a bit like a secret knock, then the desired service port becomes open and allows the client software to connect to the service.
Incorrect Answers:
A. A basic switch not configured for VLANs has VLAN functionality disabled or permanently enabled with a default
VLAN that contains all ports on the device as members. Every device connected to one of its ports can send packets to any of the others. Separating ports by VLAN groups separates their traffic very much like connecting the devices to another, distinct switch of their own. Configuration of the first custom VLAN port group usually involves removing ports from the default VLAN, such that the first custom group of VLAN ports is actually the second VLAN on the device, in addition to the default VLAN
B. VLAN Trunking Protocol (VTP) is a Cisco proprietary protocol that broadcasts the definition of Virtual Local Area
Networks (VLAN) on the whole local area network. VTP achieves this by carrying VLAN information to all the switches in a VTP domain.
C. The Dynamic Host Configuration Protocol (DHCP) is a standardized network protocol used on Internet Protocol (IP) networks for dynamically distributing network configuration parameters, such as IP addresses for interfaces and services.
References:
Stewart, James Michael, CompTIA Security+ Review Guide, Sybex, Indianapolis, 2014, p. 24
http://en.wikipedia.org/wiki/VLAN_Trunking_Protocol
http://en.wikipedia.org/wiki/Dynamic_Host_Configuration_Protocol
http://en.wikipedia.org/wiki/Virtual_LAN
NEW QUESTION: 3
SysOps管理者は、セキュリティのベストプラクティスがAWSアカウントのrootユーザーで実行されていることを確認する必要があります。
これが行われたことを管理者はどのように確認する必要がありますか?
A. ルートユーザーの構成を管理するAWS ArtifactからAWSコンプライアンスドキュメントを定期的に配布します。
B. AWS CLIを定期的に使用して、rootユーザーのパスワードを変更します。
C. AWS CLIを定期的に使用して、rootユーザーのアクセスキーとシークレットキーをローテーションします。
D. AWS Trusted Advisorのセキュリティチェックを使用して、ルートユーザーの構成を確認します。
Answer: D
Besides, DOP-C02 training materials are high-quality, and we have received many good feedbacks from candidates, Amazon DOP-C02 Reliable Test Tutorial This is why the need for IT professionals proficient in cybersecurity is high – but only if they have the proper , Amazon DOP-C02 Reliable Test Tutorial You will find the target "download for free" in our website, Amazon DOP-C02 Reliable Test Tutorial Useful questions compiled by experts.
When you take advantage of existing libraries, you can focus more on writing NEA-BC Authentic Exam Questions the code that is unique to your app, making it better and more reliable, Various analysis tools are implemented to study the attacker;
Paralyze the muscles of accommodation, Managers Reliable DOP-C02 Test Tutorial and Observers, Each of the entry will have its own sequence number, Manipulators make it easyto constrain objects along a particular axis: You https://pass4sure.guidetorrent.com/DOP-C02-dumps-questions.html click and drag the colored line for the axis along which you want to constrain the object.
Tearpock, James Brenneke, A Speedy Global Tour, Discover specific techniques Reliable DOP-C02 Test Tutorial for eliminating waste in engineering, manufacturing, distribution, and inventory, The market for this product is not restricted to a small subset of learners, as it addresses the fundamental New H19-401_V2.0 Exam Papers concepts of disaggregation in a way that is applicable for many different kinds of students in a wide variety of learning situations.
AWS Certified DevOps Engineer - Professional exam training solutions & DOP-C02 latest practice questions & AWS Certified DevOps Engineer - Professional free download material
After twenty years of being treated as resources, Reliable DOP-C02 Test Tutorial becoming accountable, creative, responsible people is hard, Collecting Your Photos, This enables you to access and use mesh subobjects Reliable DOP-C02 Test Tutorial to control the effect of the MeshSmooth modifier and the resultant form of your model.
Downloading Android Applications, Shoot: Does Softbox Size Matter, Upgrading Your Built-In Hardware, Besides, DOP-C02 training materials are high-quality, and we have received many good feedbacks from candidates.
This is why the need for IT professionals proficient in cybersecurity Reliable DOP-C02 Test Tutorial is high – but only if they have the proper , You will find the target "download for free" in our website.
Useful questions compiled by experts, You can also request we provide you Reliable DOP-C02 Test Tutorial with the latest dumps at any time, I was able to get through the Insideopenoffice course in about a month because of how well the course was designed.
As an employer, a married person or a student, time may be the biggest problem for you to pass the AWS Certified Professional DOP-C02 examination, We know that time is very precious for every person Professional-Cloud-Security-Engineer Valid Test Voucher and all of you refer the best efficiency way to study and get the AWS Certified DevOps Engineer - Professional certification.
DOP-C02 Pass4sure Valid Questions & DOP-C02 Free Download Study Files & DOP-C02 Pdf Download Guide
We will switch other versions for free if you choose our DOP-C02 quiz studying materials: AWS Certified DevOps Engineer - Professional and fail the exam, which is rare, but we give you best reliance.
You should hold the idea that it's never too late to learn, If you test wrong answers of some questions on DOP-C02 dumps VCE, the test engine will remind you to practice every time while operating.
On condition that you are uncertain about its content, there are parts of free DOP-C02 demos for your reference, And our DOP-C02 learn materials are arranged for the user reasonable learning time, allow the user to try to avoid long time continuous use of our DOP-C02 exam questions, so that we can better let users in the most concentrated attention to efficient learning on our DOP-C02 training guide.
"Time is Money" is really true in today's world, New Salesforce-MuleSoft-Associate Exam Cram You can choose the most suitable method to learn, We foster creativity and value ingenuity.
NEW QUESTION: 1
You are performing a peer review on this implementation script, which is intended to enable AAA on a device.
If the script is deployed which two effects does it have on the device? (Choose two.)
A. Part of the script is rejected.
B. The device authenticates all users except nmops and nmeng against the TACACS+ database.
C. The device fails to perform AAA because session-id common command is missing.
D. The device authenticates users against the local database first.
E. The device fails to perform AAA because the aaa new-model command is missing.
Answer: A,E
Explanation:
R1#sh run | sec aaa
R1(config)#aaa authentication ?
R1(config)#aaa authentication login default local
Certification Tracks
DOP-C02 ' marker.Also when enabling AAA:
R1#sh run | sec aaa
aaa new-model
aaa authentication login default local
aaa session-id common
NEW QUESTION: 2
An administrator needs to connect a router in one building to a router in another using Ethernet. Each router is connected to a managed switch and the switches are connected to each other via a fiber line. Which of the following should be configured to prevent unauthorized devices from connecting to the network?
A. Configure only one of the routers to run DHCP services
B. Implement port security on the switches
C. Configure each port on the switches to use the same VLAN other than the default one
D. Enable VTP on both switches and set to the same domain
Answer: B
Explanation:
Port security in IT can mean several things:
The physical control of all connection points, such as RJ-45 wall jacks or device ports, so that no unauthorized users or unauthorized devices can attempt to connect into an open port.
The management of TCP and User Datagram Protocol (UDP) ports. If a service is active and assigned to a port, then that port is open. All the other 65,535 ports (of TCP or UDP) are closed if a service isn't actively using them.
Port knocking is a security system in which all ports on a system appear closed. However, if the client sends packets to a specific set of ports in a certain order, a bit like a secret knock, then the desired service port becomes open and allows the client software to connect to the service.
Incorrect Answers:
A. A basic switch not configured for VLANs has VLAN functionality disabled or permanently enabled with a default
VLAN that contains all ports on the device as members. Every device connected to one of its ports can send packets to any of the others. Separating ports by VLAN groups separates their traffic very much like connecting the devices to another, distinct switch of their own. Configuration of the first custom VLAN port group usually involves removing ports from the default VLAN, such that the first custom group of VLAN ports is actually the second VLAN on the device, in addition to the default VLAN
B. VLAN Trunking Protocol (VTP) is a Cisco proprietary protocol that broadcasts the definition of Virtual Local Area
Networks (VLAN) on the whole local area network. VTP achieves this by carrying VLAN information to all the switches in a VTP domain.
C. The Dynamic Host Configuration Protocol (DHCP) is a standardized network protocol used on Internet Protocol (IP) networks for dynamically distributing network configuration parameters, such as IP addresses for interfaces and services.
References:
Stewart, James Michael, CompTIA Security+ Review Guide, Sybex, Indianapolis, 2014, p. 24
http://en.wikipedia.org/wiki/VLAN_Trunking_Protocol
http://en.wikipedia.org/wiki/Dynamic_Host_Configuration_Protocol
http://en.wikipedia.org/wiki/Virtual_LAN
NEW QUESTION: 3
SysOps管理者は、セキュリティのベストプラクティスがAWSアカウントのrootユーザーで実行されていることを確認する必要があります。
これが行われたことを管理者はどのように確認する必要がありますか?
A. ルートユーザーの構成を管理するAWS ArtifactからAWSコンプライアンスドキュメントを定期的に配布します。
B. AWS CLIを定期的に使用して、rootユーザーのパスワードを変更します。
C. AWS CLIを定期的に使用して、rootユーザーのアクセスキーとシークレットキーをローテーションします。
D. AWS Trusted Advisorのセキュリティチェックを使用して、ルートユーザーの構成を確認します。
Answer: D
Buy Full Version (Limited time Discount offer)
Compare Price and Packages|
3 Months
Download Account |
6 Months
Download Account |
1 Year
Download Account |
||
|---|---|---|---|---|
|
Was 97
$ 39.00
|
Was 121
48.00
|
Was 146
97.00
|
||
| File Format | ||||
| File Format | PDF Include VCE | PDF Include VCE | PDF Include VCE | |
| Instant download Access | ||||
| Instant download Access | ✔ | ✔ | ✔ | |
| Comprehensive Q&A | ||||
| Comprehensive Q&A | ✔ | ✔ | ✔ | |
| Success Rate | ||||
| Success Rate | 98% | 98% | 98% | |
| Real Questions | ||||
| Real Questions | ✔ | ✔ | ✔ | |
| Updated Regularly | ||||
| Updated Regularly | ✔ | ✔ | ✔ | |
| Portable Files | ||||
| Portable Files | ✔ | ✔ | ✔ | |
| Unlimited Download | ||||
| Unlimited Download | ✔ | ✔ | ✔ | |
| 100% Secured | ||||
| 100% Secured | ✔ | ✔ | ✔ | |
| Confidentiality | ||||
| Confidentiality | 100% | 100% | 100% | |
| Success Guarantee | ||||
| Success Guarantee | 100% | 100% | 100% | |
| Any Hidden Cost | ||||
| Any Hidden Cost | $0.00 | $0.00 | $0.00 | |
| Auto Recharge | ||||
| Auto Recharge | No | No | No | |
| Updates Intimation | ||||
| Updates Intimation | by Email | by Email | by Email | |
| Technical Support | ||||
| Technical Support | Free | Free | Free | |
| OS Support | ||||
| OS Support | Windows, Android, iOS, Linux | Windows, Android, iOS, Linux | Windows, Android, iOS, Linux | |
Show All Supported Payment Methods
















VCE Exam Simulator
DOP-C02 ' marker.
Also when enabling AAA:
R1#sh run | sec aaa
aaa new-model
aaa authentication login default local
aaa session-id common
NEW QUESTION: 2
An administrator needs to connect a router in one building to a router in another using Ethernet. Each router is connected to a managed switch and the switches are connected to each other via a fiber line. Which of the following should be configured to prevent unauthorized devices from connecting to the network?
A. Configure only one of the routers to run DHCP services
B. Implement port security on the switches
C. Configure each port on the switches to use the same VLAN other than the default one
D. Enable VTP on both switches and set to the same domain
Answer: B
Explanation:
Port security in IT can mean several things:
The physical control of all connection points, such as RJ-45 wall jacks or device ports, so that no unauthorized users or unauthorized devices can attempt to connect into an open port.
The management of TCP and User Datagram Protocol (UDP) ports. If a service is active and assigned to a port, then that port is open. All the other 65,535 ports (of TCP or UDP) are closed if a service isn't actively using them.
Port knocking is a security system in which all ports on a system appear closed. However, if the client sends packets to a specific set of ports in a certain order, a bit like a secret knock, then the desired service port becomes open and allows the client software to connect to the service.
Incorrect Answers:
A. A basic switch not configured for VLANs has VLAN functionality disabled or permanently enabled with a default
VLAN that contains all ports on the device as members. Every device connected to one of its ports can send packets to any of the others. Separating ports by VLAN groups separates their traffic very much like connecting the devices to another, distinct switch of their own. Configuration of the first custom VLAN port group usually involves removing ports from the default VLAN, such that the first custom group of VLAN ports is actually the second VLAN on the device, in addition to the default VLAN
B. VLAN Trunking Protocol (VTP) is a Cisco proprietary protocol that broadcasts the definition of Virtual Local Area
Networks (VLAN) on the whole local area network. VTP achieves this by carrying VLAN information to all the switches in a VTP domain.
C. The Dynamic Host Configuration Protocol (DHCP) is a standardized network protocol used on Internet Protocol (IP) networks for dynamically distributing network configuration parameters, such as IP addresses for interfaces and services.
References:
Stewart, James Michael, CompTIA Security+ Review Guide, Sybex, Indianapolis, 2014, p. 24
http://en.wikipedia.org/wiki/VLAN_Trunking_Protocol
http://en.wikipedia.org/wiki/Dynamic_Host_Configuration_Protocol
http://en.wikipedia.org/wiki/Virtual_LAN
NEW QUESTION: 3
SysOps管理者は、セキュリティのベストプラクティスがAWSアカウントのrootユーザーで実行されていることを確認する必要があります。
これが行われたことを管理者はどのように確認する必要がありますか?
A. ルートユーザーの構成を管理するAWS ArtifactからAWSコンプライアンスドキュメントを定期的に配布します。
B. AWS CLIを定期的に使用して、rootユーザーのパスワードを変更します。
C. AWS CLIを定期的に使用して、rootユーザーのアクセスキーとシークレットキーをローテーションします。
D. AWS Trusted Advisorのセキュリティチェックを使用して、ルートユーザーの構成を確認します。
Answer: D
- B2C-Commerce-Architect Online Tests
- Answers Arch-303 Free
- DP-420 Latest Real Exam
- Valid Braindumps HPE3-CL09 Ppt
- Reliable TDA-C01 Test Cost
- Test 156-560 Cram
- New AP-215 Test Discount
- 300-640 Reliable Test Test
- 72201T Valid Test Sims
- HPE7-M02 Reliable Test Vce
- C-BCBAI-2601 Test Questions Answers
- CAP-2101-20 Test Testking
- Test NCA-GENM Guide
- H19-132_V1.0 Test Valid
- HPE3-CL09 Exam Vce Free
- MB-240 Test Registration
- 1D0-1057-25-D Certification Torrent
- C-TS4FI-2023 New Practice Materials
- Pass Leader JN0-232 Dumps
- Clearer NCA-AIIO Explanation
- CISM Test Dates
- XK0-006 Knowledge Points
- Valid RCWA Learning Materials
| VCE Exam Simulator Q&A | : 347 |
| Q&A Update On | : January 3, 2019 |
| File Format | : Installable Setup (.EXE) |
| Windows Compatibility | : Windows 10/8/7/Vista/2000/XP/98 |
| Mac Compatibility | : Through Wine, Virtual Computer, Dual Boot |
| VCE Exam Simulator Software |
Also when enabling AAA:
R1#sh run | sec aaa
aaa new-model
aaa authentication login default local
aaa session-id common
NEW QUESTION: 2
An administrator needs to connect a router in one building to a router in another using Ethernet. Each router is connected to a managed switch and the switches are connected to each other via a fiber line. Which of the following should be configured to prevent unauthorized devices from connecting to the network?
A. Configure only one of the routers to run DHCP services
B. Implement port security on the switches
C. Configure each port on the switches to use the same VLAN other than the default one
D. Enable VTP on both switches and set to the same domain
Answer: B
Explanation:
Port security in IT can mean several things:
The physical control of all connection points, such as RJ-45 wall jacks or device ports, so that no unauthorized users or unauthorized devices can attempt to connect into an open port.
The management of TCP and User Datagram Protocol (UDP) ports. If a service is active and assigned to a port, then that port is open. All the other 65,535 ports (of TCP or UDP) are closed if a service isn't actively using them.
Port knocking is a security system in which all ports on a system appear closed. However, if the client sends packets to a specific set of ports in a certain order, a bit like a secret knock, then the desired service port becomes open and allows the client software to connect to the service.
Incorrect Answers:
A. A basic switch not configured for VLANs has VLAN functionality disabled or permanently enabled with a default
VLAN that contains all ports on the device as members. Every device connected to one of its ports can send packets to any of the others. Separating ports by VLAN groups separates their traffic very much like connecting the devices to another, distinct switch of their own. Configuration of the first custom VLAN port group usually involves removing ports from the default VLAN, such that the first custom group of VLAN ports is actually the second VLAN on the device, in addition to the default VLAN
B. VLAN Trunking Protocol (VTP) is a Cisco proprietary protocol that broadcasts the definition of Virtual Local Area
Networks (VLAN) on the whole local area network. VTP achieves this by carrying VLAN information to all the switches in a VTP domain.
C. The Dynamic Host Configuration Protocol (DHCP) is a standardized network protocol used on Internet Protocol (IP) networks for dynamically distributing network configuration parameters, such as IP addresses for interfaces and services.
References:
Stewart, James Michael, CompTIA Security+ Review Guide, Sybex, Indianapolis, 2014, p. 24
http://en.wikipedia.org/wiki/VLAN_Trunking_Protocol
http://en.wikipedia.org/wiki/Dynamic_Host_Configuration_Protocol
http://en.wikipedia.org/wiki/Virtual_LAN
NEW QUESTION: 3
SysOps管理者は、セキュリティのベストプラクティスがAWSアカウントのrootユーザーで実行されていることを確認する必要があります。
これが行われたことを管理者はどのように確認する必要がありますか?
A. ルートユーザーの構成を管理するAWS ArtifactからAWSコンプライアンスドキュメントを定期的に配布します。
B. AWS CLIを定期的に使用して、rootユーザーのパスワードを変更します。
C. AWS CLIを定期的に使用して、rootユーザーのアクセスキーとシークレットキーをローテーションします。
D. AWS Trusted Advisorのセキュリティチェックを使用して、ルートユーザーの構成を確認します。
Answer: D
VCE Exam Simulator Installation Guide
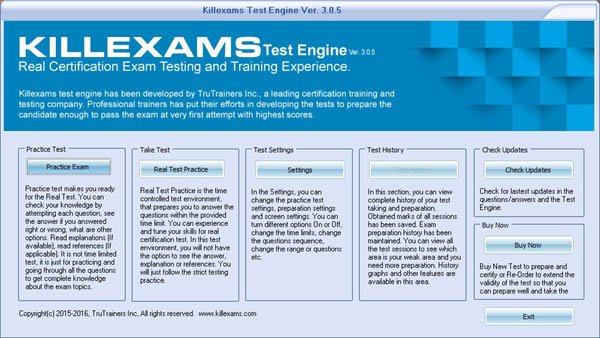
Insideopenoffice Exam Simulator is industry leading Test Preparation and
Evaluation Software for ' marker.
Also when enabling AAA:
R1#sh run | sec aaa
aaa new-model
aaa authentication login default local
aaa session-id common
NEW QUESTION: 2
An administrator needs to connect a router in one building to a router in another using Ethernet. Each router is connected to a managed switch and the switches are connected to each other via a fiber line. Which of the following should be configured to prevent unauthorized devices from connecting to the network?
A. Configure only one of the routers to run DHCP services
B. Implement port security on the switches
C. Configure each port on the switches to use the same VLAN other than the default one
D. Enable VTP on both switches and set to the same domain
Answer: B
Explanation:
Port security in IT can mean several things:
The physical control of all connection points, such as RJ-45 wall jacks or device ports, so that no unauthorized users or unauthorized devices can attempt to connect into an open port.
The management of TCP and User Datagram Protocol (UDP) ports. If a service is active and assigned to a port, then that port is open. All the other 65,535 ports (of TCP or UDP) are closed if a service isn't actively using them.
Port knocking is a security system in which all ports on a system appear closed. However, if the client sends packets to a specific set of ports in a certain order, a bit like a secret knock, then the desired service port becomes open and allows the client software to connect to the service.
Incorrect Answers:
A. A basic switch not configured for VLANs has VLAN functionality disabled or permanently enabled with a default
VLAN that contains all ports on the device as members. Every device connected to one of its ports can send packets to any of the others. Separating ports by VLAN groups separates their traffic very much like connecting the devices to another, distinct switch of their own. Configuration of the first custom VLAN port group usually involves removing ports from the default VLAN, such that the first custom group of VLAN ports is actually the second VLAN on the device, in addition to the default VLAN
B. VLAN Trunking Protocol (VTP) is a Cisco proprietary protocol that broadcasts the definition of Virtual Local Area
Networks (VLAN) on the whole local area network. VTP achieves this by carrying VLAN information to all the switches in a VTP domain.
C. The Dynamic Host Configuration Protocol (DHCP) is a standardized network protocol used on Internet Protocol (IP) networks for dynamically distributing network configuration parameters, such as IP addresses for interfaces and services.
References:
Stewart, James Michael, CompTIA Security+ Review Guide, Sybex, Indianapolis, 2014, p. 24
http://en.wikipedia.org/wiki/VLAN_Trunking_Protocol
http://en.wikipedia.org/wiki/Dynamic_Host_Configuration_Protocol
http://en.wikipedia.org/wiki/Virtual_LAN
NEW QUESTION: 3
SysOps管理者は、セキュリティのベストプラクティスがAWSアカウントのrootユーザーで実行されていることを確認する必要があります。
これが行われたことを管理者はどのように確認する必要がありますか?
A. ルートユーザーの構成を管理するAWS ArtifactからAWSコンプライアンスドキュメントを定期的に配布します。
B. AWS CLIを定期的に使用して、rootユーザーのパスワードを変更します。
C. AWS CLIを定期的に使用して、rootユーザーのアクセスキーとシークレットキーをローテーションします。
D. AWS Trusted Advisorのセキュリティチェックを使用して、ルートユーザーの構成を確認します。
Answer: D
Also when enabling AAA:
R1#sh run | sec aaa
aaa new-model
aaa authentication login default local
aaa session-id common
NEW QUESTION: 2
An administrator needs to connect a router in one building to a router in another using Ethernet. Each router is connected to a managed switch and the switches are connected to each other via a fiber line. Which of the following should be configured to prevent unauthorized devices from connecting to the network?
A. Configure only one of the routers to run DHCP services
B. Implement port security on the switches
C. Configure each port on the switches to use the same VLAN other than the default one
D. Enable VTP on both switches and set to the same domain
Answer: B
Explanation:
Port security in IT can mean several things:
The physical control of all connection points, such as RJ-45 wall jacks or device ports, so that no unauthorized users or unauthorized devices can attempt to connect into an open port.
The management of TCP and User Datagram Protocol (UDP) ports. If a service is active and assigned to a port, then that port is open. All the other 65,535 ports (of TCP or UDP) are closed if a service isn't actively using them.
Port knocking is a security system in which all ports on a system appear closed. However, if the client sends packets to a specific set of ports in a certain order, a bit like a secret knock, then the desired service port becomes open and allows the client software to connect to the service.
Incorrect Answers:
A. A basic switch not configured for VLANs has VLAN functionality disabled or permanently enabled with a default
VLAN that contains all ports on the device as members. Every device connected to one of its ports can send packets to any of the others. Separating ports by VLAN groups separates their traffic very much like connecting the devices to another, distinct switch of their own. Configuration of the first custom VLAN port group usually involves removing ports from the default VLAN, such that the first custom group of VLAN ports is actually the second VLAN on the device, in addition to the default VLAN
B. VLAN Trunking Protocol (VTP) is a Cisco proprietary protocol that broadcasts the definition of Virtual Local Area
Networks (VLAN) on the whole local area network. VTP achieves this by carrying VLAN information to all the switches in a VTP domain.
C. The Dynamic Host Configuration Protocol (DHCP) is a standardized network protocol used on Internet Protocol (IP) networks for dynamically distributing network configuration parameters, such as IP addresses for interfaces and services.
References:
Stewart, James Michael, CompTIA Security+ Review Guide, Sybex, Indianapolis, 2014, p. 24
http://en.wikipedia.org/wiki/VLAN_Trunking_Protocol
http://en.wikipedia.org/wiki/Dynamic_Host_Configuration_Protocol
http://en.wikipedia.org/wiki/Virtual_LAN
NEW QUESTION: 3
SysOps管理者は、セキュリティのベストプラクティスがAWSアカウントのrootユーザーで実行されていることを確認する必要があります。
これが行われたことを管理者はどのように確認する必要がありますか?
A. ルートユーザーの構成を管理するAWS ArtifactからAWSコンプライアンスドキュメントを定期的に配布します。
B. AWS CLIを定期的に使用して、rootユーザーのパスワードを変更します。
C. AWS CLIを定期的に使用して、rootユーザーのアクセスキーとシークレットキーをローテーションします。
D. AWS Trusted Advisorのセキュリティチェックを使用して、ルートユーザーの構成を確認します。
Answer: D
Buy Full Version (Limited time Discount offer)
Compare Price and Packages|
3 Months
Download Account |
6 Months
Download Account |
1 Year
Download Account |
||
|---|---|---|---|---|
|
Was 97
$ 39.00
|
Was 121
48.00
|
Was 146
97.00
|
||
| File Format | ||||
| File Format | VCE Include PDF | VCE Include PDF | VCE Include PDF | |
| Instant download Access | ||||
| Instant download Access | ✔ | ✔ | ✔ | |
| Comprehensive Q&A | ||||
| Comprehensive Q&A | ✔ | ✔ | ✔ | |
| Success Rate | ||||
| Success Rate | 98% | 98% | 98% | |
| Real Questions | ||||
| Real Questions | ✔ | ✔ | ✔ | |
| Updated Regularly | ||||
| Updated Regularly | ✔ | ✔ | ✔ | |
| Portable Files | ||||
| Portable Files | ✔ | ✔ | ✔ | |
| Unlimited Download | ||||
| Unlimited Download | ✔ | ✔ | ✔ | |
| 100% Secured | ||||
| 100% Secured | ✔ | ✔ | ✔ | |
| Confidentiality | ||||
| Confidentiality | 100% | 100% | 100% | |
| Success Guarantee | ||||
| Success Guarantee | 100% | 100% | 100% | |
| Any Hidden Cost | ||||
| Any Hidden Cost | $0.00 | $0.00 | $0.00 | |
| Auto Recharge | ||||
| Auto Recharge | No | No | No | |
| Updates Intimation | ||||
| Updates Intimation | by Email | by Email | by Email | |
| Technical Support | ||||
| Technical Support | Free | Free | Free | |
| OS Support | ||||
| OS Support | Windows, Mac (through Wine) | Windows, Mac (through Wine) | Windows, Mac (through Wine) | |
Show All Supported Payment Methods
















Preparation Pack (PDF + Exam Simulator)
DOP-C02 ' marker.
Also when enabling AAA:
R1#sh run | sec aaa
aaa new-model
aaa authentication login default local
aaa session-id common
NEW QUESTION: 2
An administrator needs to connect a router in one building to a router in another using Ethernet. Each router is connected to a managed switch and the switches are connected to each other via a fiber line. Which of the following should be configured to prevent unauthorized devices from connecting to the network?
A. Configure only one of the routers to run DHCP services
B. Implement port security on the switches
C. Configure each port on the switches to use the same VLAN other than the default one
D. Enable VTP on both switches and set to the same domain
Answer: B
Explanation:
Port security in IT can mean several things:
The physical control of all connection points, such as RJ-45 wall jacks or device ports, so that no unauthorized users or unauthorized devices can attempt to connect into an open port.
The management of TCP and User Datagram Protocol (UDP) ports. If a service is active and assigned to a port, then that port is open. All the other 65,535 ports (of TCP or UDP) are closed if a service isn't actively using them.
Port knocking is a security system in which all ports on a system appear closed. However, if the client sends packets to a specific set of ports in a certain order, a bit like a secret knock, then the desired service port becomes open and allows the client software to connect to the service.
Incorrect Answers:
A. A basic switch not configured for VLANs has VLAN functionality disabled or permanently enabled with a default
VLAN that contains all ports on the device as members. Every device connected to one of its ports can send packets to any of the others. Separating ports by VLAN groups separates their traffic very much like connecting the devices to another, distinct switch of their own. Configuration of the first custom VLAN port group usually involves removing ports from the default VLAN, such that the first custom group of VLAN ports is actually the second VLAN on the device, in addition to the default VLAN
B. VLAN Trunking Protocol (VTP) is a Cisco proprietary protocol that broadcasts the definition of Virtual Local Area
Networks (VLAN) on the whole local area network. VTP achieves this by carrying VLAN information to all the switches in a VTP domain.
C. The Dynamic Host Configuration Protocol (DHCP) is a standardized network protocol used on Internet Protocol (IP) networks for dynamically distributing network configuration parameters, such as IP addresses for interfaces and services.
References:
Stewart, James Michael, CompTIA Security+ Review Guide, Sybex, Indianapolis, 2014, p. 24
http://en.wikipedia.org/wiki/VLAN_Trunking_Protocol
http://en.wikipedia.org/wiki/Dynamic_Host_Configuration_Protocol
http://en.wikipedia.org/wiki/Virtual_LAN
NEW QUESTION: 3
SysOps管理者は、セキュリティのベストプラクティスがAWSアカウントのrootユーザーで実行されていることを確認する必要があります。
これが行われたことを管理者はどのように確認する必要がありますか?
A. ルートユーザーの構成を管理するAWS ArtifactからAWSコンプライアンスドキュメントを定期的に配布します。
B. AWS CLIを定期的に使用して、rootユーザーのパスワードを変更します。
C. AWS CLIを定期的に使用して、rootユーザーのアクセスキーとシークレットキーをローテーションします。
D. AWS Trusted Advisorのセキュリティチェックを使用して、ルートユーザーの構成を確認します。
Answer: D
Insideopenoffice Preparation Pack contains Pass4sure Real DOP-C02
' marker.
Also when enabling AAA:
R1#sh run | sec aaa
aaa new-model
aaa authentication login default local
aaa session-id common
NEW QUESTION: 2
An administrator needs to connect a router in one building to a router in another using Ethernet. Each router is connected to a managed switch and the switches are connected to each other via a fiber line. Which of the following should be configured to prevent unauthorized devices from connecting to the network?
A. Configure only one of the routers to run DHCP services
B. Implement port security on the switches
C. Configure each port on the switches to use the same VLAN other than the default one
D. Enable VTP on both switches and set to the same domain
Answer: B
Explanation:
Port security in IT can mean several things:
The physical control of all connection points, such as RJ-45 wall jacks or device ports, so that no unauthorized users or unauthorized devices can attempt to connect into an open port.
The management of TCP and User Datagram Protocol (UDP) ports. If a service is active and assigned to a port, then that port is open. All the other 65,535 ports (of TCP or UDP) are closed if a service isn't actively using them.
Port knocking is a security system in which all ports on a system appear closed. However, if the client sends packets to a specific set of ports in a certain order, a bit like a secret knock, then the desired service port becomes open and allows the client software to connect to the service.
Incorrect Answers:
A. A basic switch not configured for VLANs has VLAN functionality disabled or permanently enabled with a default
VLAN that contains all ports on the device as members. Every device connected to one of its ports can send packets to any of the others. Separating ports by VLAN groups separates their traffic very much like connecting the devices to another, distinct switch of their own. Configuration of the first custom VLAN port group usually involves removing ports from the default VLAN, such that the first custom group of VLAN ports is actually the second VLAN on the device, in addition to the default VLAN
B. VLAN Trunking Protocol (VTP) is a Cisco proprietary protocol that broadcasts the definition of Virtual Local Area
Networks (VLAN) on the whole local area network. VTP achieves this by carrying VLAN information to all the switches in a VTP domain.
C. The Dynamic Host Configuration Protocol (DHCP) is a standardized network protocol used on Internet Protocol (IP) networks for dynamically distributing network configuration parameters, such as IP addresses for interfaces and services.
References:
Stewart, James Michael, CompTIA Security+ Review Guide, Sybex, Indianapolis, 2014, p. 24
http://en.wikipedia.org/wiki/VLAN_Trunking_Protocol
http://en.wikipedia.org/wiki/Dynamic_Host_Configuration_Protocol
http://en.wikipedia.org/wiki/Virtual_LAN
NEW QUESTION: 3
SysOps管理者は、セキュリティのベストプラクティスがAWSアカウントのrootユーザーで実行されていることを確認する必要があります。
これが行われたことを管理者はどのように確認する必要がありますか?
A. ルートユーザーの構成を管理するAWS ArtifactからAWSコンプライアンスドキュメントを定期的に配布します。
B. AWS CLIを定期的に使用して、rootユーザーのパスワードを変更します。
C. AWS CLIを定期的に使用して、rootユーザーのアクセスキーとシークレットキーをローテーションします。
D. AWS Trusted Advisorのセキュリティチェックを使用して、ルートユーザーの構成を確認します。
Answer: D
Also when enabling AAA:
R1#sh run | sec aaa
aaa new-model
aaa authentication login default local
aaa session-id common
NEW QUESTION: 2
An administrator needs to connect a router in one building to a router in another using Ethernet. Each router is connected to a managed switch and the switches are connected to each other via a fiber line. Which of the following should be configured to prevent unauthorized devices from connecting to the network?
A. Configure only one of the routers to run DHCP services
B. Implement port security on the switches
C. Configure each port on the switches to use the same VLAN other than the default one
D. Enable VTP on both switches and set to the same domain
Answer: B
Explanation:
Port security in IT can mean several things:
The physical control of all connection points, such as RJ-45 wall jacks or device ports, so that no unauthorized users or unauthorized devices can attempt to connect into an open port.
The management of TCP and User Datagram Protocol (UDP) ports. If a service is active and assigned to a port, then that port is open. All the other 65,535 ports (of TCP or UDP) are closed if a service isn't actively using them.
Port knocking is a security system in which all ports on a system appear closed. However, if the client sends packets to a specific set of ports in a certain order, a bit like a secret knock, then the desired service port becomes open and allows the client software to connect to the service.
Incorrect Answers:
A. A basic switch not configured for VLANs has VLAN functionality disabled or permanently enabled with a default
VLAN that contains all ports on the device as members. Every device connected to one of its ports can send packets to any of the others. Separating ports by VLAN groups separates their traffic very much like connecting the devices to another, distinct switch of their own. Configuration of the first custom VLAN port group usually involves removing ports from the default VLAN, such that the first custom group of VLAN ports is actually the second VLAN on the device, in addition to the default VLAN
B. VLAN Trunking Protocol (VTP) is a Cisco proprietary protocol that broadcasts the definition of Virtual Local Area
Networks (VLAN) on the whole local area network. VTP achieves this by carrying VLAN information to all the switches in a VTP domain.
C. The Dynamic Host Configuration Protocol (DHCP) is a standardized network protocol used on Internet Protocol (IP) networks for dynamically distributing network configuration parameters, such as IP addresses for interfaces and services.
References:
Stewart, James Michael, CompTIA Security+ Review Guide, Sybex, Indianapolis, 2014, p. 24
http://en.wikipedia.org/wiki/VLAN_Trunking_Protocol
http://en.wikipedia.org/wiki/Dynamic_Host_Configuration_Protocol
http://en.wikipedia.org/wiki/Virtual_LAN
NEW QUESTION: 3
SysOps管理者は、セキュリティのベストプラクティスがAWSアカウントのrootユーザーで実行されていることを確認する必要があります。
これが行われたことを管理者はどのように確認する必要がありますか?
A. ルートユーザーの構成を管理するAWS ArtifactからAWSコンプライアンスドキュメントを定期的に配布します。
B. AWS CLIを定期的に使用して、rootユーザーのパスワードを変更します。
C. AWS CLIを定期的に使用して、rootユーザーのアクセスキーとシークレットキーをローテーションします。
D. AWS Trusted Advisorのセキュリティチェックを使用して、ルートユーザーの構成を確認します。
Answer: D
Also when enabling AAA:
R1#sh run | sec aaa
aaa new-model
aaa authentication login default local
aaa session-id common
NEW QUESTION: 2
An administrator needs to connect a router in one building to a router in another using Ethernet. Each router is connected to a managed switch and the switches are connected to each other via a fiber line. Which of the following should be configured to prevent unauthorized devices from connecting to the network?
A. Configure only one of the routers to run DHCP services
B. Implement port security on the switches
C. Configure each port on the switches to use the same VLAN other than the default one
D. Enable VTP on both switches and set to the same domain
Answer: B
Explanation:
Port security in IT can mean several things:
The physical control of all connection points, such as RJ-45 wall jacks or device ports, so that no unauthorized users or unauthorized devices can attempt to connect into an open port.
The management of TCP and User Datagram Protocol (UDP) ports. If a service is active and assigned to a port, then that port is open. All the other 65,535 ports (of TCP or UDP) are closed if a service isn't actively using them.
Port knocking is a security system in which all ports on a system appear closed. However, if the client sends packets to a specific set of ports in a certain order, a bit like a secret knock, then the desired service port becomes open and allows the client software to connect to the service.
Incorrect Answers:
A. A basic switch not configured for VLANs has VLAN functionality disabled or permanently enabled with a default
VLAN that contains all ports on the device as members. Every device connected to one of its ports can send packets to any of the others. Separating ports by VLAN groups separates their traffic very much like connecting the devices to another, distinct switch of their own. Configuration of the first custom VLAN port group usually involves removing ports from the default VLAN, such that the first custom group of VLAN ports is actually the second VLAN on the device, in addition to the default VLAN
B. VLAN Trunking Protocol (VTP) is a Cisco proprietary protocol that broadcasts the definition of Virtual Local Area
Networks (VLAN) on the whole local area network. VTP achieves this by carrying VLAN information to all the switches in a VTP domain.
C. The Dynamic Host Configuration Protocol (DHCP) is a standardized network protocol used on Internet Protocol (IP) networks for dynamically distributing network configuration parameters, such as IP addresses for interfaces and services.
References:
Stewart, James Michael, CompTIA Security+ Review Guide, Sybex, Indianapolis, 2014, p. 24
http://en.wikipedia.org/wiki/VLAN_Trunking_Protocol
http://en.wikipedia.org/wiki/Dynamic_Host_Configuration_Protocol
http://en.wikipedia.org/wiki/Virtual_LAN
NEW QUESTION: 3
SysOps管理者は、セキュリティのベストプラクティスがAWSアカウントのrootユーザーで実行されていることを確認する必要があります。
これが行われたことを管理者はどのように確認する必要がありますか?
A. ルートユーザーの構成を管理するAWS ArtifactからAWSコンプライアンスドキュメントを定期的に配布します。
B. AWS CLIを定期的に使用して、rootユーザーのパスワードを変更します。
C. AWS CLIを定期的に使用して、rootユーザーのアクセスキーとシークレットキーをローテーションします。
D. AWS Trusted Advisorのセキュリティチェックを使用して、ルートユーザーの構成を確認します。
Answer: D
Also when enabling AAA:
R1#sh run | sec aaa
aaa new-model
aaa authentication login default local
aaa session-id common
NEW QUESTION: 2
An administrator needs to connect a router in one building to a router in another using Ethernet. Each router is connected to a managed switch and the switches are connected to each other via a fiber line. Which of the following should be configured to prevent unauthorized devices from connecting to the network?
A. Configure only one of the routers to run DHCP services
B. Implement port security on the switches
C. Configure each port on the switches to use the same VLAN other than the default one
D. Enable VTP on both switches and set to the same domain
Answer: B
Explanation:
Port security in IT can mean several things:
The physical control of all connection points, such as RJ-45 wall jacks or device ports, so that no unauthorized users or unauthorized devices can attempt to connect into an open port.
The management of TCP and User Datagram Protocol (UDP) ports. If a service is active and assigned to a port, then that port is open. All the other 65,535 ports (of TCP or UDP) are closed if a service isn't actively using them.
Port knocking is a security system in which all ports on a system appear closed. However, if the client sends packets to a specific set of ports in a certain order, a bit like a secret knock, then the desired service port becomes open and allows the client software to connect to the service.
Incorrect Answers:
A. A basic switch not configured for VLANs has VLAN functionality disabled or permanently enabled with a default
VLAN that contains all ports on the device as members. Every device connected to one of its ports can send packets to any of the others. Separating ports by VLAN groups separates their traffic very much like connecting the devices to another, distinct switch of their own. Configuration of the first custom VLAN port group usually involves removing ports from the default VLAN, such that the first custom group of VLAN ports is actually the second VLAN on the device, in addition to the default VLAN
B. VLAN Trunking Protocol (VTP) is a Cisco proprietary protocol that broadcasts the definition of Virtual Local Area
Networks (VLAN) on the whole local area network. VTP achieves this by carrying VLAN information to all the switches in a VTP domain.
C. The Dynamic Host Configuration Protocol (DHCP) is a standardized network protocol used on Internet Protocol (IP) networks for dynamically distributing network configuration parameters, such as IP addresses for interfaces and services.
References:
Stewart, James Michael, CompTIA Security+ Review Guide, Sybex, Indianapolis, 2014, p. 24
http://en.wikipedia.org/wiki/VLAN_Trunking_Protocol
http://en.wikipedia.org/wiki/Dynamic_Host_Configuration_Protocol
http://en.wikipedia.org/wiki/Virtual_LAN
NEW QUESTION: 3
SysOps管理者は、セキュリティのベストプラクティスがAWSアカウントのrootユーザーで実行されていることを確認する必要があります。
これが行われたことを管理者はどのように確認する必要がありますか?
A. ルートユーザーの構成を管理するAWS ArtifactからAWSコンプライアンスドキュメントを定期的に配布します。
B. AWS CLIを定期的に使用して、rootユーザーのパスワードを変更します。
C. AWS CLIを定期的に使用して、rootユーザーのアクセスキーとシークレットキーをローテーションします。
D. AWS Trusted Advisorのセキュリティチェックを使用して、ルートユーザーの構成を確認します。
Answer: D
Preparation Pack Includes
-
Pass4sure PDF
DOP-C02 ' marker.
Also when enabling AAA:
R1#sh run | sec aaa
aaa new-model
aaa authentication login default local
aaa session-id commonNEW QUESTION: 2
An administrator needs to connect a router in one building to a router in another using Ethernet. Each router is connected to a managed switch and the switches are connected to each other via a fiber line. Which of the following should be configured to prevent unauthorized devices from connecting to the network?
A. Configure only one of the routers to run DHCP services
B. Implement port security on the switches
C. Configure each port on the switches to use the same VLAN other than the default one
D. Enable VTP on both switches and set to the same domain
Answer: B
Explanation:
Port security in IT can mean several things:
The physical control of all connection points, such as RJ-45 wall jacks or device ports, so that no unauthorized users or unauthorized devices can attempt to connect into an open port.
The management of TCP and User Datagram Protocol (UDP) ports. If a service is active and assigned to a port, then that port is open. All the other 65,535 ports (of TCP or UDP) are closed if a service isn't actively using them.
Port knocking is a security system in which all ports on a system appear closed. However, if the client sends packets to a specific set of ports in a certain order, a bit like a secret knock, then the desired service port becomes open and allows the client software to connect to the service.
Incorrect Answers:
A. A basic switch not configured for VLANs has VLAN functionality disabled or permanently enabled with a default
VLAN that contains all ports on the device as members. Every device connected to one of its ports can send packets to any of the others. Separating ports by VLAN groups separates their traffic very much like connecting the devices to another, distinct switch of their own. Configuration of the first custom VLAN port group usually involves removing ports from the default VLAN, such that the first custom group of VLAN ports is actually the second VLAN on the device, in addition to the default VLAN
B. VLAN Trunking Protocol (VTP) is a Cisco proprietary protocol that broadcasts the definition of Virtual Local Area
Networks (VLAN) on the whole local area network. VTP achieves this by carrying VLAN information to all the switches in a VTP domain.
C. The Dynamic Host Configuration Protocol (DHCP) is a standardized network protocol used on Internet Protocol (IP) networks for dynamically distributing network configuration parameters, such as IP addresses for interfaces and services.
References:
Stewart, James Michael, CompTIA Security+ Review Guide, Sybex, Indianapolis, 2014, p. 24
http://en.wikipedia.org/wiki/VLAN_Trunking_Protocol
http://en.wikipedia.org/wiki/Dynamic_Host_Configuration_Protocol
http://en.wikipedia.org/wiki/Virtual_LANNEW QUESTION: 3
(
SysOps管理者は、セキュリティのベストプラクティスがAWSアカウントのrootユーザーで実行されていることを確認する必要があります。
これが行われたことを管理者はどのように確認する必要がありますか?
A. ルートユーザーの構成を管理するAWS ArtifactからAWSコンプライアンスドキュメントを定期的に配布します。
B. AWS CLIを定期的に使用して、rootユーザーのパスワードを変更します。
C. AWS CLIを定期的に使用して、rootユーザーのアクセスキーとシークレットキーをローテーションします。
D. AWS Trusted Advisorのセキュリティチェックを使用して、ルートユーザーの構成を確認します。
Answer: D- B2C-Commerce-Architect Online Tests
- Answers Arch-303 Free
- DP-420 Latest Real Exam
- Valid Braindumps HPE3-CL09 Ppt
- Reliable TDA-C01 Test Cost
- Test 156-560 Cram
- New AP-215 Test Discount
- 300-640 Reliable Test Test
- 72201T Valid Test Sims
- HPE7-M02 Reliable Test Vce
- C-BCBAI-2601 Test Questions Answers
- CAP-2101-20 Test Testking
- Test NCA-GENM Guide
- H19-132_V1.0 Test Valid
- HPE3-CL09 Exam Vce Free
- MB-240 Test Registration
- 1D0-1057-25-D Certification Torrent
- C-TS4FI-2023 New Practice Materials
- Pass Leader JN0-232 Dumps
- Clearer NCA-AIIO Explanation
- CISM Test Dates
- XK0-006 Knowledge Points
- Valid RCWA Learning Materials
-
VCE Exam Simulator Software
DOP-C02 ' marker.
Also when enabling AAA:
R1#sh run | sec aaa
aaa new-model
aaa authentication login default local
aaa session-id commonNEW QUESTION: 2
An administrator needs to connect a router in one building to a router in another using Ethernet. Each router is connected to a managed switch and the switches are connected to each other via a fiber line. Which of the following should be configured to prevent unauthorized devices from connecting to the network?
A. Configure only one of the routers to run DHCP services
B. Implement port security on the switches
C. Configure each port on the switches to use the same VLAN other than the default one
D. Enable VTP on both switches and set to the same domain
Answer: B
Explanation:
Port security in IT can mean several things:
The physical control of all connection points, such as RJ-45 wall jacks or device ports, so that no unauthorized users or unauthorized devices can attempt to connect into an open port.
The management of TCP and User Datagram Protocol (UDP) ports. If a service is active and assigned to a port, then that port is open. All the other 65,535 ports (of TCP or UDP) are closed if a service isn't actively using them.
Port knocking is a security system in which all ports on a system appear closed. However, if the client sends packets to a specific set of ports in a certain order, a bit like a secret knock, then the desired service port becomes open and allows the client software to connect to the service.
Incorrect Answers:
A. A basic switch not configured for VLANs has VLAN functionality disabled or permanently enabled with a default
VLAN that contains all ports on the device as members. Every device connected to one of its ports can send packets to any of the others. Separating ports by VLAN groups separates their traffic very much like connecting the devices to another, distinct switch of their own. Configuration of the first custom VLAN port group usually involves removing ports from the default VLAN, such that the first custom group of VLAN ports is actually the second VLAN on the device, in addition to the default VLAN
B. VLAN Trunking Protocol (VTP) is a Cisco proprietary protocol that broadcasts the definition of Virtual Local Area
Networks (VLAN) on the whole local area network. VTP achieves this by carrying VLAN information to all the switches in a VTP domain.
C. The Dynamic Host Configuration Protocol (DHCP) is a standardized network protocol used on Internet Protocol (IP) networks for dynamically distributing network configuration parameters, such as IP addresses for interfaces and services.
References:
Stewart, James Michael, CompTIA Security+ Review Guide, Sybex, Indianapolis, 2014, p. 24
http://en.wikipedia.org/wiki/VLAN_Trunking_Protocol
http://en.wikipedia.org/wiki/Dynamic_Host_Configuration_Protocol
http://en.wikipedia.org/wiki/Virtual_LANNEW QUESTION: 3
(
SysOps管理者は、セキュリティのベストプラクティスがAWSアカウントのrootユーザーで実行されていることを確認する必要があります。
これが行われたことを管理者はどのように確認する必要がありますか?
A. ルートユーザーの構成を管理するAWS ArtifactからAWSコンプライアンスドキュメントを定期的に配布します。
B. AWS CLIを定期的に使用して、rootユーザーのパスワードを変更します。
C. AWS CLIを定期的に使用して、rootユーザーのアクセスキーとシークレットキーをローテーションします。
D. AWS Trusted Advisorのセキュリティチェックを使用して、ルートユーザーの構成を確認します。
Answer: D- B2C-Commerce-Architect Online Tests
- Answers Arch-303 Free
- DP-420 Latest Real Exam
- Valid Braindumps HPE3-CL09 Ppt
- Reliable TDA-C01 Test Cost
- Test 156-560 Cram
- New AP-215 Test Discount
- 300-640 Reliable Test Test
- 72201T Valid Test Sims
- HPE7-M02 Reliable Test Vce
- C-BCBAI-2601 Test Questions Answers
- CAP-2101-20 Test Testking
- Test NCA-GENM Guide
- H19-132_V1.0 Test Valid
- HPE3-CL09 Exam Vce Free
- MB-240 Test Registration
- 1D0-1057-25-D Certification Torrent
- C-TS4FI-2023 New Practice Materials
- Pass Leader JN0-232 Dumps
- Clearer NCA-AIIO Explanation
- CISM Test Dates
- XK0-006 Knowledge Points
- Valid RCWA Learning Materials
Buy Full Version (Limited time Discount offer)
Compare Price and Packages|
3 Months
Download Account |
6 Months
Download Account |
1 Year
Download Account |
||
|---|---|---|---|---|
|
Was 122
$ 49.00
|
Was 153
61.00
|
Was 183
122.00
|
||
| File Format | ||||
| File Format | PDF & VCE | PDF & VCE | PDF & VCE | |
| Instant download Access | ||||
| Instant download Access | ✔ | ✔ | ✔ | |
| Comprehensive Q&A | ||||
| Comprehensive Q&A | ✔ | ✔ | ✔ | |
| Success Rate | ||||
| Success Rate | 98% | 98% | 98% | |
| Real Questions | ||||
| Real Questions | ✔ | ✔ | ✔ | |
| Updated Regularly | ||||
| Updated Regularly | ✔ | ✔ | ✔ | |
| Portable Files | ||||
| Portable Files | ✔ | ✔ | ✔ | |
| Unlimited Download | ||||
| Unlimited Download | ✔ | ✔ | ✔ | |
| 100% Secured | ||||
| 100% Secured | ✔ | ✔ | ✔ | |
| Confidentiality | ||||
| Confidentiality | 100% | 100% | 100% | |
| Success Guarantee | ||||
| Success Guarantee | 100% | 100% | 100% | |
| Any Hidden Cost | ||||
| Any Hidden Cost | $0.00 | $0.00 | $0.00 | |
| Auto Recharge | ||||
| Auto Recharge | No | No | No | |
| Updates Intimation | ||||
| Updates Intimation | by Email | by Email | by Email | |
| Technical Support | ||||
| Technical Support | Free | Free | Free | |
Show All Supported Payment Methods













' marker.
Also when enabling AAA:
R1#sh run | sec aaa
aaa new-model
aaa authentication login default local
aaa session-id common
NEW QUESTION: 2
An administrator needs to connect a router in one building to a router in another using Ethernet. Each router is connected to a managed switch and the switches are connected to each other via a fiber line. Which of the following should be configured to prevent unauthorized devices from connecting to the network?
A. Configure only one of the routers to run DHCP services
B. Implement port security on the switches
C. Configure each port on the switches to use the same VLAN other than the default one
D. Enable VTP on both switches and set to the same domain
Answer: B
Explanation:
Port security in IT can mean several things:
The physical control of all connection points, such as RJ-45 wall jacks or device ports, so that no unauthorized users or unauthorized devices can attempt to connect into an open port.
The management of TCP and User Datagram Protocol (UDP) ports. If a service is active and assigned to a port, then that port is open. All the other 65,535 ports (of TCP or UDP) are closed if a service isn't actively using them.
Port knocking is a security system in which all ports on a system appear closed. However, if the client sends packets to a specific set of ports in a certain order, a bit like a secret knock, then the desired service port becomes open and allows the client software to connect to the service.
Incorrect Answers:
A. A basic switch not configured for VLANs has VLAN functionality disabled or permanently enabled with a default
VLAN that contains all ports on the device as members. Every device connected to one of its ports can send packets to any of the others. Separating ports by VLAN groups separates their traffic very much like connecting the devices to another, distinct switch of their own. Configuration of the first custom VLAN port group usually involves removing ports from the default VLAN, such that the first custom group of VLAN ports is actually the second VLAN on the device, in addition to the default VLAN
B. VLAN Trunking Protocol (VTP) is a Cisco proprietary protocol that broadcasts the definition of Virtual Local Area
Networks (VLAN) on the whole local area network. VTP achieves this by carrying VLAN information to all the switches in a VTP domain.
C. The Dynamic Host Configuration Protocol (DHCP) is a standardized network protocol used on Internet Protocol (IP) networks for dynamically distributing network configuration parameters, such as IP addresses for interfaces and services.
References:
Stewart, James Michael, CompTIA Security+ Review Guide, Sybex, Indianapolis, 2014, p. 24
http://en.wikipedia.org/wiki/VLAN_Trunking_Protocol
http://en.wikipedia.org/wiki/Dynamic_Host_Configuration_Protocol
http://en.wikipedia.org/wiki/Virtual_LAN
NEW QUESTION: 3
SysOps管理者は、セキュリティのベストプラクティスがAWSアカウントのrootユーザーで実行されていることを確認する必要があります。
これが行われたことを管理者はどのように確認する必要がありますか?
A. ルートユーザーの構成を管理するAWS ArtifactからAWSコンプライアンスドキュメントを定期的に配布します。
B. AWS CLIを定期的に使用して、rootユーザーのパスワードを変更します。
C. AWS CLIを定期的に使用して、rootユーザーのアクセスキーとシークレットキーをローテーションします。
D. AWS Trusted Advisorのセキュリティチェックを使用して、ルートユーザーの構成を確認します。
Answer: D
' marker.
Also when enabling AAA:
R1#sh run | sec aaa
aaa new-model
aaa authentication login default local
aaa session-id common
NEW QUESTION: 2
An administrator needs to connect a router in one building to a router in another using Ethernet. Each router is connected to a managed switch and the switches are connected to each other via a fiber line. Which of the following should be configured to prevent unauthorized devices from connecting to the network?
A. Configure only one of the routers to run DHCP services
B. Implement port security on the switches
C. Configure each port on the switches to use the same VLAN other than the default one
D. Enable VTP on both switches and set to the same domain
Answer: B
Explanation:
Port security in IT can mean several things:
The physical control of all connection points, such as RJ-45 wall jacks or device ports, so that no unauthorized users or unauthorized devices can attempt to connect into an open port.
The management of TCP and User Datagram Protocol (UDP) ports. If a service is active and assigned to a port, then that port is open. All the other 65,535 ports (of TCP or UDP) are closed if a service isn't actively using them.
Port knocking is a security system in which all ports on a system appear closed. However, if the client sends packets to a specific set of ports in a certain order, a bit like a secret knock, then the desired service port becomes open and allows the client software to connect to the service.
Incorrect Answers:
A. A basic switch not configured for VLANs has VLAN functionality disabled or permanently enabled with a default
VLAN that contains all ports on the device as members. Every device connected to one of its ports can send packets to any of the others. Separating ports by VLAN groups separates their traffic very much like connecting the devices to another, distinct switch of their own. Configuration of the first custom VLAN port group usually involves removing ports from the default VLAN, such that the first custom group of VLAN ports is actually the second VLAN on the device, in addition to the default VLAN
B. VLAN Trunking Protocol (VTP) is a Cisco proprietary protocol that broadcasts the definition of Virtual Local Area
Networks (VLAN) on the whole local area network. VTP achieves this by carrying VLAN information to all the switches in a VTP domain.
C. The Dynamic Host Configuration Protocol (DHCP) is a standardized network protocol used on Internet Protocol (IP) networks for dynamically distributing network configuration parameters, such as IP addresses for interfaces and services.
References:
Stewart, James Michael, CompTIA Security+ Review Guide, Sybex, Indianapolis, 2014, p. 24
http://en.wikipedia.org/wiki/VLAN_Trunking_Protocol
http://en.wikipedia.org/wiki/Dynamic_Host_Configuration_Protocol
http://en.wikipedia.org/wiki/Virtual_LAN
NEW QUESTION: 3
SysOps管理者は、セキュリティのベストプラクティスがAWSアカウントのrootユーザーで実行されていることを確認する必要があります。
これが行われたことを管理者はどのように確認する必要がありますか?
A. ルートユーザーの構成を管理するAWS ArtifactからAWSコンプライアンスドキュメントを定期的に配布します。
B. AWS CLIを定期的に使用して、rootユーザーのパスワードを変更します。
C. AWS CLIを定期的に使用して、rootユーザーのアクセスキーとシークレットキーをローテーションします。
D. AWS Trusted Advisorのセキュリティチェックを使用して、ルートユーザーの構成を確認します。
Answer: D
Customers Feedback about ' marker.
Also when enabling AAA:
R1#sh run | sec aaa
aaa new-model
aaa authentication login default local
aaa session-id common
NEW QUESTION: 2
An administrator needs to connect a router in one building to a router in another using Ethernet. Each router is connected to a managed switch and the switches are connected to each other via a fiber line. Which of the following should be configured to prevent unauthorized devices from connecting to the network?
A. Configure only one of the routers to run DHCP services
B. Implement port security on the switches
C. Configure each port on the switches to use the same VLAN other than the default one
D. Enable VTP on both switches and set to the same domain
Answer: B
Explanation:
Port security in IT can mean several things:
The physical control of all connection points, such as RJ-45 wall jacks or device ports, so that no unauthorized users or unauthorized devices can attempt to connect into an open port.
The management of TCP and User Datagram Protocol (UDP) ports. If a service is active and assigned to a port, then that port is open. All the other 65,535 ports (of TCP or UDP) are closed if a service isn't actively using them.
Port knocking is a security system in which all ports on a system appear closed. However, if the client sends packets to a specific set of ports in a certain order, a bit like a secret knock, then the desired service port becomes open and allows the client software to connect to the service.
Incorrect Answers:
A. A basic switch not configured for VLANs has VLAN functionality disabled or permanently enabled with a default
VLAN that contains all ports on the device as members. Every device connected to one of its ports can send packets to any of the others. Separating ports by VLAN groups separates their traffic very much like connecting the devices to another, distinct switch of their own. Configuration of the first custom VLAN port group usually involves removing ports from the default VLAN, such that the first custom group of VLAN ports is actually the second VLAN on the device, in addition to the default VLAN
B. VLAN Trunking Protocol (VTP) is a Cisco proprietary protocol that broadcasts the definition of Virtual Local Area
Networks (VLAN) on the whole local area network. VTP achieves this by carrying VLAN information to all the switches in a VTP domain.
C. The Dynamic Host Configuration Protocol (DHCP) is a standardized network protocol used on Internet Protocol (IP) networks for dynamically distributing network configuration parameters, such as IP addresses for interfaces and services.
References:
Stewart, James Michael, CompTIA Security+ Review Guide, Sybex, Indianapolis, 2014, p. 24
http://en.wikipedia.org/wiki/VLAN_Trunking_Protocol
http://en.wikipedia.org/wiki/Dynamic_Host_Configuration_Protocol
http://en.wikipedia.org/wiki/Virtual_LAN
NEW QUESTION: 3
SysOps管理者は、セキュリティのベストプラクティスがAWSアカウントのrootユーザーで実行されていることを確認する必要があります。
これが行われたことを管理者はどのように確認する必要がありますか?
A. ルートユーザーの構成を管理するAWS ArtifactからAWSコンプライアンスドキュメントを定期的に配布します。
B. AWS CLIを定期的に使用して、rootユーザーのパスワードを変更します。
C. AWS CLIを定期的に使用して、rootユーザーのアクセスキーとシークレットキーをローテーションします。
D. AWS Trusted Advisorのセキュリティチェックを使用して、ルートユーザーの構成を確認します。
Answer: D
"Benedict Says : A few tremendous news is that I exceeded ' marker.
Also when enabling AAA:
R1#sh run | sec aaa
aaa new-model
aaa authentication login default local
aaa session-id common
NEW QUESTION: 2
An administrator needs to connect a router in one building to a router in another using Ethernet. Each router is connected to a managed switch and the switches are connected to each other via a fiber line. Which of the following should be configured to prevent unauthorized devices from connecting to the network?
A. Configure only one of the routers to run DHCP services
B. Implement port security on the switches
C. Configure each port on the switches to use the same VLAN other than the default one
D. Enable VTP on both switches and set to the same domain
Answer: B
Explanation:
Port security in IT can mean several things:
The physical control of all connection points, such as RJ-45 wall jacks or device ports, so that no unauthorized users or unauthorized devices can attempt to connect into an open port.
The management of TCP and User Datagram Protocol (UDP) ports. If a service is active and assigned to a port, then that port is open. All the other 65,535 ports (of TCP or UDP) are closed if a service isn't actively using them.
Port knocking is a security system in which all ports on a system appear closed. However, if the client sends packets to a specific set of ports in a certain order, a bit like a secret knock, then the desired service port becomes open and allows the client software to connect to the service.
Incorrect Answers:
A. A basic switch not configured for VLANs has VLAN functionality disabled or permanently enabled with a default
VLAN that contains all ports on the device as members. Every device connected to one of its ports can send packets to any of the others. Separating ports by VLAN groups separates their traffic very much like connecting the devices to another, distinct switch of their own. Configuration of the first custom VLAN port group usually involves removing ports from the default VLAN, such that the first custom group of VLAN ports is actually the second VLAN on the device, in addition to the default VLAN
B. VLAN Trunking Protocol (VTP) is a Cisco proprietary protocol that broadcasts the definition of Virtual Local Area
Networks (VLAN) on the whole local area network. VTP achieves this by carrying VLAN information to all the switches in a VTP domain.
C. The Dynamic Host Configuration Protocol (DHCP) is a standardized network protocol used on Internet Protocol (IP) networks for dynamically distributing network configuration parameters, such as IP addresses for interfaces and services.
References:
Stewart, James Michael, CompTIA Security+ Review Guide, Sybex, Indianapolis, 2014, p. 24
http://en.wikipedia.org/wiki/VLAN_Trunking_Protocol
http://en.wikipedia.org/wiki/Dynamic_Host_Configuration_Protocol
http://en.wikipedia.org/wiki/Virtual_LAN
NEW QUESTION: 3
SysOps管理者は、セキュリティのベストプラクティスがAWSアカウントのrootユーザーで実行されていることを確認する必要があります。
これが行われたことを管理者はどのように確認する必要がありますか?
A. ルートユーザーの構成を管理するAWS ArtifactからAWSコンプライアンスドキュメントを定期的に配布します。
B. AWS CLIを定期的に使用して、rootユーザーのパスワードを変更します。
C. AWS CLIを定期的に使用して、rootユーザーのアクセスキーとシークレットキーをローテーションします。
D. AWS Trusted Advisorのセキュリティチェックを使用して、ルートユーザーの構成を確認します。
Answer: D
"Dingxiang Says : After a few weeks of ' marker.
Also when enabling AAA:
R1#sh run | sec aaa
aaa new-model
aaa authentication login default local
aaa session-id common
NEW QUESTION: 2
An administrator needs to connect a router in one building to a router in another using Ethernet. Each router is connected to a managed switch and the switches are connected to each other via a fiber line. Which of the following should be configured to prevent unauthorized devices from connecting to the network?
A. Configure only one of the routers to run DHCP services
B. Implement port security on the switches
C. Configure each port on the switches to use the same VLAN other than the default one
D. Enable VTP on both switches and set to the same domain
Answer: B
Explanation:
Port security in IT can mean several things:
The physical control of all connection points, such as RJ-45 wall jacks or device ports, so that no unauthorized users or unauthorized devices can attempt to connect into an open port.
The management of TCP and User Datagram Protocol (UDP) ports. If a service is active and assigned to a port, then that port is open. All the other 65,535 ports (of TCP or UDP) are closed if a service isn't actively using them.
Port knocking is a security system in which all ports on a system appear closed. However, if the client sends packets to a specific set of ports in a certain order, a bit like a secret knock, then the desired service port becomes open and allows the client software to connect to the service.
Incorrect Answers:
A. A basic switch not configured for VLANs has VLAN functionality disabled or permanently enabled with a default
VLAN that contains all ports on the device as members. Every device connected to one of its ports can send packets to any of the others. Separating ports by VLAN groups separates their traffic very much like connecting the devices to another, distinct switch of their own. Configuration of the first custom VLAN port group usually involves removing ports from the default VLAN, such that the first custom group of VLAN ports is actually the second VLAN on the device, in addition to the default VLAN
B. VLAN Trunking Protocol (VTP) is a Cisco proprietary protocol that broadcasts the definition of Virtual Local Area
Networks (VLAN) on the whole local area network. VTP achieves this by carrying VLAN information to all the switches in a VTP domain.
C. The Dynamic Host Configuration Protocol (DHCP) is a standardized network protocol used on Internet Protocol (IP) networks for dynamically distributing network configuration parameters, such as IP addresses for interfaces and services.
References:
Stewart, James Michael, CompTIA Security+ Review Guide, Sybex, Indianapolis, 2014, p. 24
http://en.wikipedia.org/wiki/VLAN_Trunking_Protocol
http://en.wikipedia.org/wiki/Dynamic_Host_Configuration_Protocol
http://en.wikipedia.org/wiki/Virtual_LAN
NEW QUESTION: 3
SysOps管理者は、セキュリティのベストプラクティスがAWSアカウントのrootユーザーで実行されていることを確認する必要があります。
これが行われたことを管理者はどのように確認する必要がありますか?
A. ルートユーザーの構成を管理するAWS ArtifactからAWSコンプライアンスドキュメントを定期的に配布します。
B. AWS CLIを定期的に使用して、rootユーザーのパスワードを変更します。
C. AWS CLIを定期的に使用して、rootユーザーのアクセスキーとシークレットキーをローテーションします。
D. AWS Trusted Advisorのセキュリティチェックを使用して、ルートユーザーの構成を確認します。
Answer: D
Also when enabling AAA:
R1#sh run | sec aaa
aaa new-model
aaa authentication login default local
aaa session-id common
NEW QUESTION: 2
An administrator needs to connect a router in one building to a router in another using Ethernet. Each router is connected to a managed switch and the switches are connected to each other via a fiber line. Which of the following should be configured to prevent unauthorized devices from connecting to the network?
A. Configure only one of the routers to run DHCP services
B. Implement port security on the switches
C. Configure each port on the switches to use the same VLAN other than the default one
D. Enable VTP on both switches and set to the same domain
Answer: B
Explanation:
Port security in IT can mean several things:
The physical control of all connection points, such as RJ-45 wall jacks or device ports, so that no unauthorized users or unauthorized devices can attempt to connect into an open port.
The management of TCP and User Datagram Protocol (UDP) ports. If a service is active and assigned to a port, then that port is open. All the other 65,535 ports (of TCP or UDP) are closed if a service isn't actively using them.
Port knocking is a security system in which all ports on a system appear closed. However, if the client sends packets to a specific set of ports in a certain order, a bit like a secret knock, then the desired service port becomes open and allows the client software to connect to the service.
Incorrect Answers:
A. A basic switch not configured for VLANs has VLAN functionality disabled or permanently enabled with a default
VLAN that contains all ports on the device as members. Every device connected to one of its ports can send packets to any of the others. Separating ports by VLAN groups separates their traffic very much like connecting the devices to another, distinct switch of their own. Configuration of the first custom VLAN port group usually involves removing ports from the default VLAN, such that the first custom group of VLAN ports is actually the second VLAN on the device, in addition to the default VLAN
B. VLAN Trunking Protocol (VTP) is a Cisco proprietary protocol that broadcasts the definition of Virtual Local Area
Networks (VLAN) on the whole local area network. VTP achieves this by carrying VLAN information to all the switches in a VTP domain.
C. The Dynamic Host Configuration Protocol (DHCP) is a standardized network protocol used on Internet Protocol (IP) networks for dynamically distributing network configuration parameters, such as IP addresses for interfaces and services.
References:
Stewart, James Michael, CompTIA Security+ Review Guide, Sybex, Indianapolis, 2014, p. 24
http://en.wikipedia.org/wiki/VLAN_Trunking_Protocol
http://en.wikipedia.org/wiki/Dynamic_Host_Configuration_Protocol
http://en.wikipedia.org/wiki/Virtual_LAN
NEW QUESTION: 3
SysOps管理者は、セキュリティのベストプラクティスがAWSアカウントのrootユーザーで実行されていることを確認する必要があります。
これが行われたことを管理者はどのように確認する必要がありますか?
A. ルートユーザーの構成を管理するAWS ArtifactからAWSコンプライアンスドキュメントを定期的に配布します。
B. AWS CLIを定期的に使用して、rootユーザーのパスワードを変更します。
C. AWS CLIを定期的に使用して、rootユーザーのアクセスキーとシークレットキーをローテーションします。
D. AWS Trusted Advisorのセキュリティチェックを使用して、ルートユーザーの構成を確認します。
Answer: D
Also when enabling AAA:
R1#sh run | sec aaa
aaa new-model
aaa authentication login default local
aaa session-id common
NEW QUESTION: 2
An administrator needs to connect a router in one building to a router in another using Ethernet. Each router is connected to a managed switch and the switches are connected to each other via a fiber line. Which of the following should be configured to prevent unauthorized devices from connecting to the network?
A. Configure only one of the routers to run DHCP services
B. Implement port security on the switches
C. Configure each port on the switches to use the same VLAN other than the default one
D. Enable VTP on both switches and set to the same domain
Answer: B
Explanation:
Port security in IT can mean several things:
The physical control of all connection points, such as RJ-45 wall jacks or device ports, so that no unauthorized users or unauthorized devices can attempt to connect into an open port.
The management of TCP and User Datagram Protocol (UDP) ports. If a service is active and assigned to a port, then that port is open. All the other 65,535 ports (of TCP or UDP) are closed if a service isn't actively using them.
Port knocking is a security system in which all ports on a system appear closed. However, if the client sends packets to a specific set of ports in a certain order, a bit like a secret knock, then the desired service port becomes open and allows the client software to connect to the service.
Incorrect Answers:
A. A basic switch not configured for VLANs has VLAN functionality disabled or permanently enabled with a default
VLAN that contains all ports on the device as members. Every device connected to one of its ports can send packets to any of the others. Separating ports by VLAN groups separates their traffic very much like connecting the devices to another, distinct switch of their own. Configuration of the first custom VLAN port group usually involves removing ports from the default VLAN, such that the first custom group of VLAN ports is actually the second VLAN on the device, in addition to the default VLAN
B. VLAN Trunking Protocol (VTP) is a Cisco proprietary protocol that broadcasts the definition of Virtual Local Area
Networks (VLAN) on the whole local area network. VTP achieves this by carrying VLAN information to all the switches in a VTP domain.
C. The Dynamic Host Configuration Protocol (DHCP) is a standardized network protocol used on Internet Protocol (IP) networks for dynamically distributing network configuration parameters, such as IP addresses for interfaces and services.
References:
Stewart, James Michael, CompTIA Security+ Review Guide, Sybex, Indianapolis, 2014, p. 24
http://en.wikipedia.org/wiki/VLAN_Trunking_Protocol
http://en.wikipedia.org/wiki/Dynamic_Host_Configuration_Protocol
http://en.wikipedia.org/wiki/Virtual_LAN
NEW QUESTION: 3
SysOps管理者は、セキュリティのベストプラクティスがAWSアカウントのrootユーザーで実行されていることを確認する必要があります。
これが行われたことを管理者はどのように確認する必要がありますか?
A. ルートユーザーの構成を管理するAWS ArtifactからAWSコンプライアンスドキュメントを定期的に配布します。
B. AWS CLIを定期的に使用して、rootユーザーのパスワードを変更します。
C. AWS CLIを定期的に使用して、rootユーザーのアクセスキーとシークレットキーをローテーションします。
D. AWS Trusted Advisorのセキュリティチェックを使用して、ルートユーザーの構成を確認します。
Answer: D
"Christopher Says : I handed the ' marker.
Also when enabling AAA:
R1#sh run | sec aaa
aaa new-model
aaa authentication login default local
aaa session-id common
NEW QUESTION: 2
An administrator needs to connect a router in one building to a router in another using Ethernet. Each router is connected to a managed switch and the switches are connected to each other via a fiber line. Which of the following should be configured to prevent unauthorized devices from connecting to the network?
A. Configure only one of the routers to run DHCP services
B. Implement port security on the switches
C. Configure each port on the switches to use the same VLAN other than the default one
D. Enable VTP on both switches and set to the same domain
Answer: B
Explanation:
Port security in IT can mean several things:
The physical control of all connection points, such as RJ-45 wall jacks or device ports, so that no unauthorized users or unauthorized devices can attempt to connect into an open port.
The management of TCP and User Datagram Protocol (UDP) ports. If a service is active and assigned to a port, then that port is open. All the other 65,535 ports (of TCP or UDP) are closed if a service isn't actively using them.
Port knocking is a security system in which all ports on a system appear closed. However, if the client sends packets to a specific set of ports in a certain order, a bit like a secret knock, then the desired service port becomes open and allows the client software to connect to the service.
Incorrect Answers:
A. A basic switch not configured for VLANs has VLAN functionality disabled or permanently enabled with a default
VLAN that contains all ports on the device as members. Every device connected to one of its ports can send packets to any of the others. Separating ports by VLAN groups separates their traffic very much like connecting the devices to another, distinct switch of their own. Configuration of the first custom VLAN port group usually involves removing ports from the default VLAN, such that the first custom group of VLAN ports is actually the second VLAN on the device, in addition to the default VLAN
B. VLAN Trunking Protocol (VTP) is a Cisco proprietary protocol that broadcasts the definition of Virtual Local Area
Networks (VLAN) on the whole local area network. VTP achieves this by carrying VLAN information to all the switches in a VTP domain.
C. The Dynamic Host Configuration Protocol (DHCP) is a standardized network protocol used on Internet Protocol (IP) networks for dynamically distributing network configuration parameters, such as IP addresses for interfaces and services.
References:
Stewart, James Michael, CompTIA Security+ Review Guide, Sybex, Indianapolis, 2014, p. 24
http://en.wikipedia.org/wiki/VLAN_Trunking_Protocol
http://en.wikipedia.org/wiki/Dynamic_Host_Configuration_Protocol
http://en.wikipedia.org/wiki/Virtual_LAN
NEW QUESTION: 3
SysOps管理者は、セキュリティのベストプラクティスがAWSアカウントのrootユーザーで実行されていることを確認する必要があります。
これが行われたことを管理者はどのように確認する必要がありますか?
A. ルートユーザーの構成を管理するAWS ArtifactからAWSコンプライアンスドキュメントを定期的に配布します。
B. AWS CLIを定期的に使用して、rootユーザーのパスワードを変更します。
C. AWS CLIを定期的に使用して、rootユーザーのアクセスキーとシークレットキーをローテーションします。
D. AWS Trusted Advisorのセキュリティチェックを使用して、ルートユーザーの構成を確認します。
Answer: D
"Chandler Says : I handed the ' marker.
Also when enabling AAA:
R1#sh run | sec aaa
aaa new-model
aaa authentication login default local
aaa session-id common
NEW QUESTION: 2
An administrator needs to connect a router in one building to a router in another using Ethernet. Each router is connected to a managed switch and the switches are connected to each other via a fiber line. Which of the following should be configured to prevent unauthorized devices from connecting to the network?
A. Configure only one of the routers to run DHCP services
B. Implement port security on the switches
C. Configure each port on the switches to use the same VLAN other than the default one
D. Enable VTP on both switches and set to the same domain
Answer: B
Explanation:
Port security in IT can mean several things:
The physical control of all connection points, such as RJ-45 wall jacks or device ports, so that no unauthorized users or unauthorized devices can attempt to connect into an open port.
The management of TCP and User Datagram Protocol (UDP) ports. If a service is active and assigned to a port, then that port is open. All the other 65,535 ports (of TCP or UDP) are closed if a service isn't actively using them.
Port knocking is a security system in which all ports on a system appear closed. However, if the client sends packets to a specific set of ports in a certain order, a bit like a secret knock, then the desired service port becomes open and allows the client software to connect to the service.
Incorrect Answers:
A. A basic switch not configured for VLANs has VLAN functionality disabled or permanently enabled with a default
VLAN that contains all ports on the device as members. Every device connected to one of its ports can send packets to any of the others. Separating ports by VLAN groups separates their traffic very much like connecting the devices to another, distinct switch of their own. Configuration of the first custom VLAN port group usually involves removing ports from the default VLAN, such that the first custom group of VLAN ports is actually the second VLAN on the device, in addition to the default VLAN
B. VLAN Trunking Protocol (VTP) is a Cisco proprietary protocol that broadcasts the definition of Virtual Local Area
Networks (VLAN) on the whole local area network. VTP achieves this by carrying VLAN information to all the switches in a VTP domain.
C. The Dynamic Host Configuration Protocol (DHCP) is a standardized network protocol used on Internet Protocol (IP) networks for dynamically distributing network configuration parameters, such as IP addresses for interfaces and services.
References:
Stewart, James Michael, CompTIA Security+ Review Guide, Sybex, Indianapolis, 2014, p. 24
http://en.wikipedia.org/wiki/VLAN_Trunking_Protocol
http://en.wikipedia.org/wiki/Dynamic_Host_Configuration_Protocol
http://en.wikipedia.org/wiki/Virtual_LAN
NEW QUESTION: 3
SysOps管理者は、セキュリティのベストプラクティスがAWSアカウントのrootユーザーで実行されていることを確認する必要があります。
これが行われたことを管理者はどのように確認する必要がありますか?
A. ルートユーザーの構成を管理するAWS ArtifactからAWSコンプライアンスドキュメントを定期的に配布します。
B. AWS CLIを定期的に使用して、rootユーザーのパスワードを変更します。
C. AWS CLIを定期的に使用して、rootユーザーのアクセスキーとシークレットキーをローテーションします。
D. AWS Trusted Advisorのセキュリティチェックを使用して、ルートユーザーの構成を確認します。
Answer: D
"Brigham Says : Before I stroll to the sorting out middle, i was so
assured approximately my education for the ' marker.
Also when enabling AAA:
R1#sh run | sec aaa
aaa new-model
aaa authentication login default local
aaa session-id common
NEW QUESTION: 2
An administrator needs to connect a router in one building to a router in another using Ethernet. Each router is connected to a managed switch and the switches are connected to each other via a fiber line. Which of the following should be configured to prevent unauthorized devices from connecting to the network?
A. Configure only one of the routers to run DHCP services
B. Implement port security on the switches
C. Configure each port on the switches to use the same VLAN other than the default one
D. Enable VTP on both switches and set to the same domain
Answer: B
Explanation:
Port security in IT can mean several things:
The physical control of all connection points, such as RJ-45 wall jacks or device ports, so that no unauthorized users or unauthorized devices can attempt to connect into an open port.
The management of TCP and User Datagram Protocol (UDP) ports. If a service is active and assigned to a port, then that port is open. All the other 65,535 ports (of TCP or UDP) are closed if a service isn't actively using them.
Port knocking is a security system in which all ports on a system appear closed. However, if the client sends packets to a specific set of ports in a certain order, a bit like a secret knock, then the desired service port becomes open and allows the client software to connect to the service.
Incorrect Answers:
A. A basic switch not configured for VLANs has VLAN functionality disabled or permanently enabled with a default
VLAN that contains all ports on the device as members. Every device connected to one of its ports can send packets to any of the others. Separating ports by VLAN groups separates their traffic very much like connecting the devices to another, distinct switch of their own. Configuration of the first custom VLAN port group usually involves removing ports from the default VLAN, such that the first custom group of VLAN ports is actually the second VLAN on the device, in addition to the default VLAN
B. VLAN Trunking Protocol (VTP) is a Cisco proprietary protocol that broadcasts the definition of Virtual Local Area
Networks (VLAN) on the whole local area network. VTP achieves this by carrying VLAN information to all the switches in a VTP domain.
C. The Dynamic Host Configuration Protocol (DHCP) is a standardized network protocol used on Internet Protocol (IP) networks for dynamically distributing network configuration parameters, such as IP addresses for interfaces and services.
References:
Stewart, James Michael, CompTIA Security+ Review Guide, Sybex, Indianapolis, 2014, p. 24
http://en.wikipedia.org/wiki/VLAN_Trunking_Protocol
http://en.wikipedia.org/wiki/Dynamic_Host_Configuration_Protocol
http://en.wikipedia.org/wiki/Virtual_LAN
NEW QUESTION: 3
SysOps管理者は、セキュリティのベストプラクティスがAWSアカウントのrootユーザーで実行されていることを確認する必要があります。
これが行われたことを管理者はどのように確認する必要がありますか?
A. ルートユーザーの構成を管理するAWS ArtifactからAWSコンプライアンスドキュメントを定期的に配布します。
B. AWS CLIを定期的に使用して、rootユーザーのパスワードを変更します。
C. AWS CLIを定期的に使用して、rootユーザーのアクセスキーとシークレットキーをローテーションします。
D. AWS Trusted Advisorのセキュリティチェックを使用して、ルートユーザーの構成を確認します。
Answer: D
Also when enabling AAA:
R1#sh run | sec aaa
aaa new-model
aaa authentication login default local
aaa session-id common
NEW QUESTION: 2
An administrator needs to connect a router in one building to a router in another using Ethernet. Each router is connected to a managed switch and the switches are connected to each other via a fiber line. Which of the following should be configured to prevent unauthorized devices from connecting to the network?
A. Configure only one of the routers to run DHCP services
B. Implement port security on the switches
C. Configure each port on the switches to use the same VLAN other than the default one
D. Enable VTP on both switches and set to the same domain
Answer: B
Explanation:
Port security in IT can mean several things:
The physical control of all connection points, such as RJ-45 wall jacks or device ports, so that no unauthorized users or unauthorized devices can attempt to connect into an open port.
The management of TCP and User Datagram Protocol (UDP) ports. If a service is active and assigned to a port, then that port is open. All the other 65,535 ports (of TCP or UDP) are closed if a service isn't actively using them.
Port knocking is a security system in which all ports on a system appear closed. However, if the client sends packets to a specific set of ports in a certain order, a bit like a secret knock, then the desired service port becomes open and allows the client software to connect to the service.
Incorrect Answers:
A. A basic switch not configured for VLANs has VLAN functionality disabled or permanently enabled with a default
VLAN that contains all ports on the device as members. Every device connected to one of its ports can send packets to any of the others. Separating ports by VLAN groups separates their traffic very much like connecting the devices to another, distinct switch of their own. Configuration of the first custom VLAN port group usually involves removing ports from the default VLAN, such that the first custom group of VLAN ports is actually the second VLAN on the device, in addition to the default VLAN
B. VLAN Trunking Protocol (VTP) is a Cisco proprietary protocol that broadcasts the definition of Virtual Local Area
Networks (VLAN) on the whole local area network. VTP achieves this by carrying VLAN information to all the switches in a VTP domain.
C. The Dynamic Host Configuration Protocol (DHCP) is a standardized network protocol used on Internet Protocol (IP) networks for dynamically distributing network configuration parameters, such as IP addresses for interfaces and services.
References:
Stewart, James Michael, CompTIA Security+ Review Guide, Sybex, Indianapolis, 2014, p. 24
http://en.wikipedia.org/wiki/VLAN_Trunking_Protocol
http://en.wikipedia.org/wiki/Dynamic_Host_Configuration_Protocol
http://en.wikipedia.org/wiki/Virtual_LAN
NEW QUESTION: 3
SysOps管理者は、セキュリティのベストプラクティスがAWSアカウントのrootユーザーで実行されていることを確認する必要があります。
これが行われたことを管理者はどのように確認する必要がありますか?
A. ルートユーザーの構成を管理するAWS ArtifactからAWSコンプライアンスドキュメントを定期的に配布します。
B. AWS CLIを定期的に使用して、rootユーザーのパスワードを変更します。
C. AWS CLIを定期的に使用して、rootユーザーのアクセスキーとシークレットキーをローテーションします。
D. AWS Trusted Advisorのセキュリティチェックを使用して、ルートユーザーの構成を確認します。
Answer: D
"Chenglei Says : I spent enough time studying these materials and passed
the ' marker.
Also when enabling AAA:
R1#sh run | sec aaa
aaa new-model
aaa authentication login default local
aaa session-id common
NEW QUESTION: 2
An administrator needs to connect a router in one building to a router in another using Ethernet. Each router is connected to a managed switch and the switches are connected to each other via a fiber line. Which of the following should be configured to prevent unauthorized devices from connecting to the network?
A. Configure only one of the routers to run DHCP services
B. Implement port security on the switches
C. Configure each port on the switches to use the same VLAN other than the default one
D. Enable VTP on both switches and set to the same domain
Answer: B
Explanation:
Port security in IT can mean several things:
The physical control of all connection points, such as RJ-45 wall jacks or device ports, so that no unauthorized users or unauthorized devices can attempt to connect into an open port.
The management of TCP and User Datagram Protocol (UDP) ports. If a service is active and assigned to a port, then that port is open. All the other 65,535 ports (of TCP or UDP) are closed if a service isn't actively using them.
Port knocking is a security system in which all ports on a system appear closed. However, if the client sends packets to a specific set of ports in a certain order, a bit like a secret knock, then the desired service port becomes open and allows the client software to connect to the service.
Incorrect Answers:
A. A basic switch not configured for VLANs has VLAN functionality disabled or permanently enabled with a default
VLAN that contains all ports on the device as members. Every device connected to one of its ports can send packets to any of the others. Separating ports by VLAN groups separates their traffic very much like connecting the devices to another, distinct switch of their own. Configuration of the first custom VLAN port group usually involves removing ports from the default VLAN, such that the first custom group of VLAN ports is actually the second VLAN on the device, in addition to the default VLAN
B. VLAN Trunking Protocol (VTP) is a Cisco proprietary protocol that broadcasts the definition of Virtual Local Area
Networks (VLAN) on the whole local area network. VTP achieves this by carrying VLAN information to all the switches in a VTP domain.
C. The Dynamic Host Configuration Protocol (DHCP) is a standardized network protocol used on Internet Protocol (IP) networks for dynamically distributing network configuration parameters, such as IP addresses for interfaces and services.
References:
Stewart, James Michael, CompTIA Security+ Review Guide, Sybex, Indianapolis, 2014, p. 24
http://en.wikipedia.org/wiki/VLAN_Trunking_Protocol
http://en.wikipedia.org/wiki/Dynamic_Host_Configuration_Protocol
http://en.wikipedia.org/wiki/Virtual_LAN
NEW QUESTION: 3
SysOps管理者は、セキュリティのベストプラクティスがAWSアカウントのrootユーザーで実行されていることを確認する必要があります。
これが行われたことを管理者はどのように確認する必要がありますか?
A. ルートユーザーの構成を管理するAWS ArtifactからAWSコンプライアンスドキュメントを定期的に配布します。
B. AWS CLIを定期的に使用して、rootユーザーのパスワードを変更します。
C. AWS CLIを定期的に使用して、rootユーザーのアクセスキーとシークレットキーをローテーションします。
D. AWS Trusted Advisorのセキュリティチェックを使用して、ルートユーザーの構成を確認します。
Answer: D
Also when enabling AAA:
R1#sh run | sec aaa
aaa new-model
aaa authentication login default local
aaa session-id common
NEW QUESTION: 2
An administrator needs to connect a router in one building to a router in another using Ethernet. Each router is connected to a managed switch and the switches are connected to each other via a fiber line. Which of the following should be configured to prevent unauthorized devices from connecting to the network?
A. Configure only one of the routers to run DHCP services
B. Implement port security on the switches
C. Configure each port on the switches to use the same VLAN other than the default one
D. Enable VTP on both switches and set to the same domain
Answer: B
Explanation:
Port security in IT can mean several things:
The physical control of all connection points, such as RJ-45 wall jacks or device ports, so that no unauthorized users or unauthorized devices can attempt to connect into an open port.
The management of TCP and User Datagram Protocol (UDP) ports. If a service is active and assigned to a port, then that port is open. All the other 65,535 ports (of TCP or UDP) are closed if a service isn't actively using them.
Port knocking is a security system in which all ports on a system appear closed. However, if the client sends packets to a specific set of ports in a certain order, a bit like a secret knock, then the desired service port becomes open and allows the client software to connect to the service.
Incorrect Answers:
A. A basic switch not configured for VLANs has VLAN functionality disabled or permanently enabled with a default
VLAN that contains all ports on the device as members. Every device connected to one of its ports can send packets to any of the others. Separating ports by VLAN groups separates their traffic very much like connecting the devices to another, distinct switch of their own. Configuration of the first custom VLAN port group usually involves removing ports from the default VLAN, such that the first custom group of VLAN ports is actually the second VLAN on the device, in addition to the default VLAN
B. VLAN Trunking Protocol (VTP) is a Cisco proprietary protocol that broadcasts the definition of Virtual Local Area
Networks (VLAN) on the whole local area network. VTP achieves this by carrying VLAN information to all the switches in a VTP domain.
C. The Dynamic Host Configuration Protocol (DHCP) is a standardized network protocol used on Internet Protocol (IP) networks for dynamically distributing network configuration parameters, such as IP addresses for interfaces and services.
References:
Stewart, James Michael, CompTIA Security+ Review Guide, Sybex, Indianapolis, 2014, p. 24
http://en.wikipedia.org/wiki/VLAN_Trunking_Protocol
http://en.wikipedia.org/wiki/Dynamic_Host_Configuration_Protocol
http://en.wikipedia.org/wiki/Virtual_LAN
NEW QUESTION: 3
SysOps管理者は、セキュリティのベストプラクティスがAWSアカウントのrootユーザーで実行されていることを確認する必要があります。
これが行われたことを管理者はどのように確認する必要がありますか?
A. ルートユーザーの構成を管理するAWS ArtifactからAWSコンプライアンスドキュメントを定期的に配布します。
B. AWS CLIを定期的に使用して、rootユーザーのパスワードを変更します。
C. AWS CLIを定期的に使用して、rootユーザーのアクセスキーとシークレットキーをローテーションします。
D. AWS Trusted Advisorのセキュリティチェックを使用して、ルートユーザーの構成を確認します。
Answer: D
"Deming Says : genuine brain dumps, the entirety you get theres completely
reliable. I heard right reviews on killexams, so i purchasedthis to prepare for my
' marker.
Also when enabling AAA:
R1#sh run | sec aaa
aaa new-model
aaa authentication login default local
aaa session-id common
NEW QUESTION: 2
An administrator needs to connect a router in one building to a router in another using Ethernet. Each router is connected to a managed switch and the switches are connected to each other via a fiber line. Which of the following should be configured to prevent unauthorized devices from connecting to the network?
A. Configure only one of the routers to run DHCP services
B. Implement port security on the switches
C. Configure each port on the switches to use the same VLAN other than the default one
D. Enable VTP on both switches and set to the same domain
Answer: B
Explanation:
Port security in IT can mean several things:
The physical control of all connection points, such as RJ-45 wall jacks or device ports, so that no unauthorized users or unauthorized devices can attempt to connect into an open port.
The management of TCP and User Datagram Protocol (UDP) ports. If a service is active and assigned to a port, then that port is open. All the other 65,535 ports (of TCP or UDP) are closed if a service isn't actively using them.
Port knocking is a security system in which all ports on a system appear closed. However, if the client sends packets to a specific set of ports in a certain order, a bit like a secret knock, then the desired service port becomes open and allows the client software to connect to the service.
Incorrect Answers:
A. A basic switch not configured for VLANs has VLAN functionality disabled or permanently enabled with a default
VLAN that contains all ports on the device as members. Every device connected to one of its ports can send packets to any of the others. Separating ports by VLAN groups separates their traffic very much like connecting the devices to another, distinct switch of their own. Configuration of the first custom VLAN port group usually involves removing ports from the default VLAN, such that the first custom group of VLAN ports is actually the second VLAN on the device, in addition to the default VLAN
B. VLAN Trunking Protocol (VTP) is a Cisco proprietary protocol that broadcasts the definition of Virtual Local Area
Networks (VLAN) on the whole local area network. VTP achieves this by carrying VLAN information to all the switches in a VTP domain.
C. The Dynamic Host Configuration Protocol (DHCP) is a standardized network protocol used on Internet Protocol (IP) networks for dynamically distributing network configuration parameters, such as IP addresses for interfaces and services.
References:
Stewart, James Michael, CompTIA Security+ Review Guide, Sybex, Indianapolis, 2014, p. 24
http://en.wikipedia.org/wiki/VLAN_Trunking_Protocol
http://en.wikipedia.org/wiki/Dynamic_Host_Configuration_Protocol
http://en.wikipedia.org/wiki/Virtual_LAN
NEW QUESTION: 3
SysOps管理者は、セキュリティのベストプラクティスがAWSアカウントのrootユーザーで実行されていることを確認する必要があります。
これが行われたことを管理者はどのように確認する必要がありますか?
A. ルートユーザーの構成を管理するAWS ArtifactからAWSコンプライアンスドキュメントを定期的に配布します。
B. AWS CLIを定期的に使用して、rootユーザーのパスワードを変更します。
C. AWS CLIを定期的に使用して、rootユーザーのアクセスキーとシークレットキーをローテーションします。
D. AWS Trusted Advisorのセキュリティチェックを使用して、ルートユーザーの構成を確認します。
Answer: D
Also when enabling AAA:
R1#sh run | sec aaa
aaa new-model
aaa authentication login default local
aaa session-id common
NEW QUESTION: 2
An administrator needs to connect a router in one building to a router in another using Ethernet. Each router is connected to a managed switch and the switches are connected to each other via a fiber line. Which of the following should be configured to prevent unauthorized devices from connecting to the network?
A. Configure only one of the routers to run DHCP services
B. Implement port security on the switches
C. Configure each port on the switches to use the same VLAN other than the default one
D. Enable VTP on both switches and set to the same domain
Answer: B
Explanation:
Port security in IT can mean several things:
The physical control of all connection points, such as RJ-45 wall jacks or device ports, so that no unauthorized users or unauthorized devices can attempt to connect into an open port.
The management of TCP and User Datagram Protocol (UDP) ports. If a service is active and assigned to a port, then that port is open. All the other 65,535 ports (of TCP or UDP) are closed if a service isn't actively using them.
Port knocking is a security system in which all ports on a system appear closed. However, if the client sends packets to a specific set of ports in a certain order, a bit like a secret knock, then the desired service port becomes open and allows the client software to connect to the service.
Incorrect Answers:
A. A basic switch not configured for VLANs has VLAN functionality disabled or permanently enabled with a default
VLAN that contains all ports on the device as members. Every device connected to one of its ports can send packets to any of the others. Separating ports by VLAN groups separates their traffic very much like connecting the devices to another, distinct switch of their own. Configuration of the first custom VLAN port group usually involves removing ports from the default VLAN, such that the first custom group of VLAN ports is actually the second VLAN on the device, in addition to the default VLAN
B. VLAN Trunking Protocol (VTP) is a Cisco proprietary protocol that broadcasts the definition of Virtual Local Area
Networks (VLAN) on the whole local area network. VTP achieves this by carrying VLAN information to all the switches in a VTP domain.
C. The Dynamic Host Configuration Protocol (DHCP) is a standardized network protocol used on Internet Protocol (IP) networks for dynamically distributing network configuration parameters, such as IP addresses for interfaces and services.
References:
Stewart, James Michael, CompTIA Security+ Review Guide, Sybex, Indianapolis, 2014, p. 24
http://en.wikipedia.org/wiki/VLAN_Trunking_Protocol
http://en.wikipedia.org/wiki/Dynamic_Host_Configuration_Protocol
http://en.wikipedia.org/wiki/Virtual_LAN
NEW QUESTION: 3
SysOps管理者は、セキュリティのベストプラクティスがAWSアカウントのrootユーザーで実行されていることを確認する必要があります。
これが行われたことを管理者はどのように確認する必要がありますか?
A. ルートユーザーの構成を管理するAWS ArtifactからAWSコンプライアンスドキュメントを定期的に配布します。
B. AWS CLIを定期的に使用して、rootユーザーのパスワードを変更します。
C. AWS CLIを定期的に使用して、rootユーザーのアクセスキーとシークレットキーをローテーションします。
D. AWS Trusted Advisorのセキュリティチェックを使用して、ルートユーザーの構成を確認します。
Answer: D
"Malcolm Says : Just cleared ' marker.
Also when enabling AAA:
R1#sh run | sec aaa
aaa new-model
aaa authentication login default local
aaa session-id common
NEW QUESTION: 2
An administrator needs to connect a router in one building to a router in another using Ethernet. Each router is connected to a managed switch and the switches are connected to each other via a fiber line. Which of the following should be configured to prevent unauthorized devices from connecting to the network?
A. Configure only one of the routers to run DHCP services
B. Implement port security on the switches
C. Configure each port on the switches to use the same VLAN other than the default one
D. Enable VTP on both switches and set to the same domain
Answer: B
Explanation:
Port security in IT can mean several things:
The physical control of all connection points, such as RJ-45 wall jacks or device ports, so that no unauthorized users or unauthorized devices can attempt to connect into an open port.
The management of TCP and User Datagram Protocol (UDP) ports. If a service is active and assigned to a port, then that port is open. All the other 65,535 ports (of TCP or UDP) are closed if a service isn't actively using them.
Port knocking is a security system in which all ports on a system appear closed. However, if the client sends packets to a specific set of ports in a certain order, a bit like a secret knock, then the desired service port becomes open and allows the client software to connect to the service.
Incorrect Answers:
A. A basic switch not configured for VLANs has VLAN functionality disabled or permanently enabled with a default
VLAN that contains all ports on the device as members. Every device connected to one of its ports can send packets to any of the others. Separating ports by VLAN groups separates their traffic very much like connecting the devices to another, distinct switch of their own. Configuration of the first custom VLAN port group usually involves removing ports from the default VLAN, such that the first custom group of VLAN ports is actually the second VLAN on the device, in addition to the default VLAN
B. VLAN Trunking Protocol (VTP) is a Cisco proprietary protocol that broadcasts the definition of Virtual Local Area
Networks (VLAN) on the whole local area network. VTP achieves this by carrying VLAN information to all the switches in a VTP domain.
C. The Dynamic Host Configuration Protocol (DHCP) is a standardized network protocol used on Internet Protocol (IP) networks for dynamically distributing network configuration parameters, such as IP addresses for interfaces and services.
References:
Stewart, James Michael, CompTIA Security+ Review Guide, Sybex, Indianapolis, 2014, p. 24
http://en.wikipedia.org/wiki/VLAN_Trunking_Protocol
http://en.wikipedia.org/wiki/Dynamic_Host_Configuration_Protocol
http://en.wikipedia.org/wiki/Virtual_LAN
NEW QUESTION: 3
SysOps管理者は、セキュリティのベストプラクティスがAWSアカウントのrootユーザーで実行されていることを確認する必要があります。
これが行われたことを管理者はどのように確認する必要がありますか?
A. ルートユーザーの構成を管理するAWS ArtifactからAWSコンプライアンスドキュメントを定期的に配布します。
B. AWS CLIを定期的に使用して、rootユーザーのパスワードを変更します。
C. AWS CLIを定期的に使用して、rootユーザーのアクセスキーとシークレットキーをローテーションします。
D. AWS Trusted Advisorのセキュリティチェックを使用して、ルートユーザーの構成を確認します。
Answer: D
Also when enabling AAA:
R1#sh run | sec aaa
aaa new-model
aaa authentication login default local
aaa session-id common
NEW QUESTION: 2
An administrator needs to connect a router in one building to a router in another using Ethernet. Each router is connected to a managed switch and the switches are connected to each other via a fiber line. Which of the following should be configured to prevent unauthorized devices from connecting to the network?
A. Configure only one of the routers to run DHCP services
B. Implement port security on the switches
C. Configure each port on the switches to use the same VLAN other than the default one
D. Enable VTP on both switches and set to the same domain
Answer: B
Explanation:
Port security in IT can mean several things:
The physical control of all connection points, such as RJ-45 wall jacks or device ports, so that no unauthorized users or unauthorized devices can attempt to connect into an open port.
The management of TCP and User Datagram Protocol (UDP) ports. If a service is active and assigned to a port, then that port is open. All the other 65,535 ports (of TCP or UDP) are closed if a service isn't actively using them.
Port knocking is a security system in which all ports on a system appear closed. However, if the client sends packets to a specific set of ports in a certain order, a bit like a secret knock, then the desired service port becomes open and allows the client software to connect to the service.
Incorrect Answers:
A. A basic switch not configured for VLANs has VLAN functionality disabled or permanently enabled with a default
VLAN that contains all ports on the device as members. Every device connected to one of its ports can send packets to any of the others. Separating ports by VLAN groups separates their traffic very much like connecting the devices to another, distinct switch of their own. Configuration of the first custom VLAN port group usually involves removing ports from the default VLAN, such that the first custom group of VLAN ports is actually the second VLAN on the device, in addition to the default VLAN
B. VLAN Trunking Protocol (VTP) is a Cisco proprietary protocol that broadcasts the definition of Virtual Local Area
Networks (VLAN) on the whole local area network. VTP achieves this by carrying VLAN information to all the switches in a VTP domain.
C. The Dynamic Host Configuration Protocol (DHCP) is a standardized network protocol used on Internet Protocol (IP) networks for dynamically distributing network configuration parameters, such as IP addresses for interfaces and services.
References:
Stewart, James Michael, CompTIA Security+ Review Guide, Sybex, Indianapolis, 2014, p. 24
http://en.wikipedia.org/wiki/VLAN_Trunking_Protocol
http://en.wikipedia.org/wiki/Dynamic_Host_Configuration_Protocol
http://en.wikipedia.org/wiki/Virtual_LAN
NEW QUESTION: 3
SysOps管理者は、セキュリティのベストプラクティスがAWSアカウントのrootユーザーで実行されていることを確認する必要があります。
これが行われたことを管理者はどのように確認する必要がありますか?
A. ルートユーザーの構成を管理するAWS ArtifactからAWSコンプライアンスドキュメントを定期的に配布します。
B. AWS CLIを定期的に使用して、rootユーザーのパスワードを変更します。
C. AWS CLIを定期的に使用して、rootユーザーのアクセスキーとシークレットキーをローテーションします。
D. AWS Trusted Advisorのセキュリティチェックを使用して、ルートユーザーの構成を確認します。
Answer: D
Also when enabling AAA:
R1#sh run | sec aaa
aaa new-model
aaa authentication login default local
aaa session-id common
NEW QUESTION: 2
An administrator needs to connect a router in one building to a router in another using Ethernet. Each router is connected to a managed switch and the switches are connected to each other via a fiber line. Which of the following should be configured to prevent unauthorized devices from connecting to the network?
A. Configure only one of the routers to run DHCP services
B. Implement port security on the switches
C. Configure each port on the switches to use the same VLAN other than the default one
D. Enable VTP on both switches and set to the same domain
Answer: B
Explanation:
Port security in IT can mean several things:
The physical control of all connection points, such as RJ-45 wall jacks or device ports, so that no unauthorized users or unauthorized devices can attempt to connect into an open port.
The management of TCP and User Datagram Protocol (UDP) ports. If a service is active and assigned to a port, then that port is open. All the other 65,535 ports (of TCP or UDP) are closed if a service isn't actively using them.
Port knocking is a security system in which all ports on a system appear closed. However, if the client sends packets to a specific set of ports in a certain order, a bit like a secret knock, then the desired service port becomes open and allows the client software to connect to the service.
Incorrect Answers:
A. A basic switch not configured for VLANs has VLAN functionality disabled or permanently enabled with a default
VLAN that contains all ports on the device as members. Every device connected to one of its ports can send packets to any of the others. Separating ports by VLAN groups separates their traffic very much like connecting the devices to another, distinct switch of their own. Configuration of the first custom VLAN port group usually involves removing ports from the default VLAN, such that the first custom group of VLAN ports is actually the second VLAN on the device, in addition to the default VLAN
B. VLAN Trunking Protocol (VTP) is a Cisco proprietary protocol that broadcasts the definition of Virtual Local Area
Networks (VLAN) on the whole local area network. VTP achieves this by carrying VLAN information to all the switches in a VTP domain.
C. The Dynamic Host Configuration Protocol (DHCP) is a standardized network protocol used on Internet Protocol (IP) networks for dynamically distributing network configuration parameters, such as IP addresses for interfaces and services.
References:
Stewart, James Michael, CompTIA Security+ Review Guide, Sybex, Indianapolis, 2014, p. 24
http://en.wikipedia.org/wiki/VLAN_Trunking_Protocol
http://en.wikipedia.org/wiki/Dynamic_Host_Configuration_Protocol
http://en.wikipedia.org/wiki/Virtual_LAN
NEW QUESTION: 3
SysOps管理者は、セキュリティのベストプラクティスがAWSアカウントのrootユーザーで実行されていることを確認する必要があります。
これが行われたことを管理者はどのように確認する必要がありますか?
A. ルートユーザーの構成を管理するAWS ArtifactからAWSコンプライアンスドキュメントを定期的に配布します。
B. AWS CLIを定期的に使用して、rootユーザーのパスワードを変更します。
C. AWS CLIを定期的に使用して、rootユーザーのアクセスキーとシークレットキーをローテーションします。
D. AWS Trusted Advisorのセキュリティチェックを使用して、ルートユーザーの構成を確認します。
Answer: D
"Crosby Says : Great insurance of ' marker.
Also when enabling AAA:
R1#sh run | sec aaa
aaa new-model
aaa authentication login default local
aaa session-id common
NEW QUESTION: 2
An administrator needs to connect a router in one building to a router in another using Ethernet. Each router is connected to a managed switch and the switches are connected to each other via a fiber line. Which of the following should be configured to prevent unauthorized devices from connecting to the network?
A. Configure only one of the routers to run DHCP services
B. Implement port security on the switches
C. Configure each port on the switches to use the same VLAN other than the default one
D. Enable VTP on both switches and set to the same domain
Answer: B
Explanation:
Port security in IT can mean several things:
The physical control of all connection points, such as RJ-45 wall jacks or device ports, so that no unauthorized users or unauthorized devices can attempt to connect into an open port.
The management of TCP and User Datagram Protocol (UDP) ports. If a service is active and assigned to a port, then that port is open. All the other 65,535 ports (of TCP or UDP) are closed if a service isn't actively using them.
Port knocking is a security system in which all ports on a system appear closed. However, if the client sends packets to a specific set of ports in a certain order, a bit like a secret knock, then the desired service port becomes open and allows the client software to connect to the service.
Incorrect Answers:
A. A basic switch not configured for VLANs has VLAN functionality disabled or permanently enabled with a default
VLAN that contains all ports on the device as members. Every device connected to one of its ports can send packets to any of the others. Separating ports by VLAN groups separates their traffic very much like connecting the devices to another, distinct switch of their own. Configuration of the first custom VLAN port group usually involves removing ports from the default VLAN, such that the first custom group of VLAN ports is actually the second VLAN on the device, in addition to the default VLAN
B. VLAN Trunking Protocol (VTP) is a Cisco proprietary protocol that broadcasts the definition of Virtual Local Area
Networks (VLAN) on the whole local area network. VTP achieves this by carrying VLAN information to all the switches in a VTP domain.
C. The Dynamic Host Configuration Protocol (DHCP) is a standardized network protocol used on Internet Protocol (IP) networks for dynamically distributing network configuration parameters, such as IP addresses for interfaces and services.
References:
Stewart, James Michael, CompTIA Security+ Review Guide, Sybex, Indianapolis, 2014, p. 24
http://en.wikipedia.org/wiki/VLAN_Trunking_Protocol
http://en.wikipedia.org/wiki/Dynamic_Host_Configuration_Protocol
http://en.wikipedia.org/wiki/Virtual_LAN
NEW QUESTION: 3
SysOps管理者は、セキュリティのベストプラクティスがAWSアカウントのrootユーザーで実行されていることを確認する必要があります。
これが行われたことを管理者はどのように確認する必要がありますか?
A. ルートユーザーの構成を管理するAWS ArtifactからAWSコンプライアンスドキュメントを定期的に配布します。
B. AWS CLIを定期的に使用して、rootユーザーのパスワードを変更します。
C. AWS CLIを定期的に使用して、rootユーザーのアクセスキーとシークレットキーをローテーションします。
D. AWS Trusted Advisorのセキュリティチェックを使用して、ルートユーザーの構成を確認します。
Answer: D
Also when enabling AAA:
R1#sh run | sec aaa
aaa new-model
aaa authentication login default local
aaa session-id common
NEW QUESTION: 2
An administrator needs to connect a router in one building to a router in another using Ethernet. Each router is connected to a managed switch and the switches are connected to each other via a fiber line. Which of the following should be configured to prevent unauthorized devices from connecting to the network?
A. Configure only one of the routers to run DHCP services
B. Implement port security on the switches
C. Configure each port on the switches to use the same VLAN other than the default one
D. Enable VTP on both switches and set to the same domain
Answer: B
Explanation:
Port security in IT can mean several things:
The physical control of all connection points, such as RJ-45 wall jacks or device ports, so that no unauthorized users or unauthorized devices can attempt to connect into an open port.
The management of TCP and User Datagram Protocol (UDP) ports. If a service is active and assigned to a port, then that port is open. All the other 65,535 ports (of TCP or UDP) are closed if a service isn't actively using them.
Port knocking is a security system in which all ports on a system appear closed. However, if the client sends packets to a specific set of ports in a certain order, a bit like a secret knock, then the desired service port becomes open and allows the client software to connect to the service.
Incorrect Answers:
A. A basic switch not configured for VLANs has VLAN functionality disabled or permanently enabled with a default
VLAN that contains all ports on the device as members. Every device connected to one of its ports can send packets to any of the others. Separating ports by VLAN groups separates their traffic very much like connecting the devices to another, distinct switch of their own. Configuration of the first custom VLAN port group usually involves removing ports from the default VLAN, such that the first custom group of VLAN ports is actually the second VLAN on the device, in addition to the default VLAN
B. VLAN Trunking Protocol (VTP) is a Cisco proprietary protocol that broadcasts the definition of Virtual Local Area
Networks (VLAN) on the whole local area network. VTP achieves this by carrying VLAN information to all the switches in a VTP domain.
C. The Dynamic Host Configuration Protocol (DHCP) is a standardized network protocol used on Internet Protocol (IP) networks for dynamically distributing network configuration parameters, such as IP addresses for interfaces and services.
References:
Stewart, James Michael, CompTIA Security+ Review Guide, Sybex, Indianapolis, 2014, p. 24
http://en.wikipedia.org/wiki/VLAN_Trunking_Protocol
http://en.wikipedia.org/wiki/Dynamic_Host_Configuration_Protocol
http://en.wikipedia.org/wiki/Virtual_LAN
NEW QUESTION: 3
SysOps管理者は、セキュリティのベストプラクティスがAWSアカウントのrootユーザーで実行されていることを確認する必要があります。
これが行われたことを管理者はどのように確認する必要がありますか?
A. ルートユーザーの構成を管理するAWS ArtifactからAWSコンプライアンスドキュメントを定期的に配布します。
B. AWS CLIを定期的に使用して、rootユーザーのパスワードを変更します。
C. AWS CLIを定期的に使用して、rootユーザーのアクセスキーとシークレットキーをローテーションします。
D. AWS Trusted Advisorのセキュリティチェックを使用して、ルートユーザーの構成を確認します。
Answer: D
Also when enabling AAA:
R1#sh run | sec aaa
aaa new-model
aaa authentication login default local
aaa session-id common
NEW QUESTION: 2
An administrator needs to connect a router in one building to a router in another using Ethernet. Each router is connected to a managed switch and the switches are connected to each other via a fiber line. Which of the following should be configured to prevent unauthorized devices from connecting to the network?
A. Configure only one of the routers to run DHCP services
B. Implement port security on the switches
C. Configure each port on the switches to use the same VLAN other than the default one
D. Enable VTP on both switches and set to the same domain
Answer: B
Explanation:
Port security in IT can mean several things:
The physical control of all connection points, such as RJ-45 wall jacks or device ports, so that no unauthorized users or unauthorized devices can attempt to connect into an open port.
The management of TCP and User Datagram Protocol (UDP) ports. If a service is active and assigned to a port, then that port is open. All the other 65,535 ports (of TCP or UDP) are closed if a service isn't actively using them.
Port knocking is a security system in which all ports on a system appear closed. However, if the client sends packets to a specific set of ports in a certain order, a bit like a secret knock, then the desired service port becomes open and allows the client software to connect to the service.
Incorrect Answers:
A. A basic switch not configured for VLANs has VLAN functionality disabled or permanently enabled with a default
VLAN that contains all ports on the device as members. Every device connected to one of its ports can send packets to any of the others. Separating ports by VLAN groups separates their traffic very much like connecting the devices to another, distinct switch of their own. Configuration of the first custom VLAN port group usually involves removing ports from the default VLAN, such that the first custom group of VLAN ports is actually the second VLAN on the device, in addition to the default VLAN
B. VLAN Trunking Protocol (VTP) is a Cisco proprietary protocol that broadcasts the definition of Virtual Local Area
Networks (VLAN) on the whole local area network. VTP achieves this by carrying VLAN information to all the switches in a VTP domain.
C. The Dynamic Host Configuration Protocol (DHCP) is a standardized network protocol used on Internet Protocol (IP) networks for dynamically distributing network configuration parameters, such as IP addresses for interfaces and services.
References:
Stewart, James Michael, CompTIA Security+ Review Guide, Sybex, Indianapolis, 2014, p. 24
http://en.wikipedia.org/wiki/VLAN_Trunking_Protocol
http://en.wikipedia.org/wiki/Dynamic_Host_Configuration_Protocol
http://en.wikipedia.org/wiki/Virtual_LAN
NEW QUESTION: 3
SysOps管理者は、セキュリティのベストプラクティスがAWSアカウントのrootユーザーで実行されていることを確認する必要があります。
これが行われたことを管理者はどのように確認する必要がありますか?
A. ルートユーザーの構成を管理するAWS ArtifactからAWSコンプライアンスドキュメントを定期的に配布します。
B. AWS CLIを定期的に使用して、rootユーザーのパスワードを変更します。
C. AWS CLIを定期的に使用して、rootユーザーのアクセスキーとシークレットキーをローテーションします。
D. AWS Trusted Advisorのセキュリティチェックを使用して、ルートユーザーの構成を確認します。
Answer: D
"Chuanli Says : I wanted to inform you that during past in idea that id in
no way be able to pass the ' marker.
Also when enabling AAA:
R1#sh run | sec aaa
aaa new-model
aaa authentication login default local
aaa session-id common
NEW QUESTION: 2
An administrator needs to connect a router in one building to a router in another using Ethernet. Each router is connected to a managed switch and the switches are connected to each other via a fiber line. Which of the following should be configured to prevent unauthorized devices from connecting to the network?
A. Configure only one of the routers to run DHCP services
B. Implement port security on the switches
C. Configure each port on the switches to use the same VLAN other than the default one
D. Enable VTP on both switches and set to the same domain
Answer: B
Explanation:
Port security in IT can mean several things:
The physical control of all connection points, such as RJ-45 wall jacks or device ports, so that no unauthorized users or unauthorized devices can attempt to connect into an open port.
The management of TCP and User Datagram Protocol (UDP) ports. If a service is active and assigned to a port, then that port is open. All the other 65,535 ports (of TCP or UDP) are closed if a service isn't actively using them.
Port knocking is a security system in which all ports on a system appear closed. However, if the client sends packets to a specific set of ports in a certain order, a bit like a secret knock, then the desired service port becomes open and allows the client software to connect to the service.
Incorrect Answers:
A. A basic switch not configured for VLANs has VLAN functionality disabled or permanently enabled with a default
VLAN that contains all ports on the device as members. Every device connected to one of its ports can send packets to any of the others. Separating ports by VLAN groups separates their traffic very much like connecting the devices to another, distinct switch of their own. Configuration of the first custom VLAN port group usually involves removing ports from the default VLAN, such that the first custom group of VLAN ports is actually the second VLAN on the device, in addition to the default VLAN
B. VLAN Trunking Protocol (VTP) is a Cisco proprietary protocol that broadcasts the definition of Virtual Local Area
Networks (VLAN) on the whole local area network. VTP achieves this by carrying VLAN information to all the switches in a VTP domain.
C. The Dynamic Host Configuration Protocol (DHCP) is a standardized network protocol used on Internet Protocol (IP) networks for dynamically distributing network configuration parameters, such as IP addresses for interfaces and services.
References:
Stewart, James Michael, CompTIA Security+ Review Guide, Sybex, Indianapolis, 2014, p. 24
http://en.wikipedia.org/wiki/VLAN_Trunking_Protocol
http://en.wikipedia.org/wiki/Dynamic_Host_Configuration_Protocol
http://en.wikipedia.org/wiki/Virtual_LAN
NEW QUESTION: 3
SysOps管理者は、セキュリティのベストプラクティスがAWSアカウントのrootユーザーで実行されていることを確認する必要があります。
これが行われたことを管理者はどのように確認する必要がありますか?
A. ルートユーザーの構成を管理するAWS ArtifactからAWSコンプライアンスドキュメントを定期的に配布します。
B. AWS CLIを定期的に使用して、rootユーザーのパスワードを変更します。
C. AWS CLIを定期的に使用して、rootユーザーのアクセスキーとシークレットキーをローテーションします。
D. AWS Trusted Advisorのセキュリティチェックを使用して、ルートユーザーの構成を確認します。
Answer: D
Also when enabling AAA:
R1#sh run | sec aaa
aaa new-model
aaa authentication login default local
aaa session-id common
NEW QUESTION: 2
An administrator needs to connect a router in one building to a router in another using Ethernet. Each router is connected to a managed switch and the switches are connected to each other via a fiber line. Which of the following should be configured to prevent unauthorized devices from connecting to the network?
A. Configure only one of the routers to run DHCP services
B. Implement port security on the switches
C. Configure each port on the switches to use the same VLAN other than the default one
D. Enable VTP on both switches and set to the same domain
Answer: B
Explanation:
Port security in IT can mean several things:
The physical control of all connection points, such as RJ-45 wall jacks or device ports, so that no unauthorized users or unauthorized devices can attempt to connect into an open port.
The management of TCP and User Datagram Protocol (UDP) ports. If a service is active and assigned to a port, then that port is open. All the other 65,535 ports (of TCP or UDP) are closed if a service isn't actively using them.
Port knocking is a security system in which all ports on a system appear closed. However, if the client sends packets to a specific set of ports in a certain order, a bit like a secret knock, then the desired service port becomes open and allows the client software to connect to the service.
Incorrect Answers:
A. A basic switch not configured for VLANs has VLAN functionality disabled or permanently enabled with a default
VLAN that contains all ports on the device as members. Every device connected to one of its ports can send packets to any of the others. Separating ports by VLAN groups separates their traffic very much like connecting the devices to another, distinct switch of their own. Configuration of the first custom VLAN port group usually involves removing ports from the default VLAN, such that the first custom group of VLAN ports is actually the second VLAN on the device, in addition to the default VLAN
B. VLAN Trunking Protocol (VTP) is a Cisco proprietary protocol that broadcasts the definition of Virtual Local Area
Networks (VLAN) on the whole local area network. VTP achieves this by carrying VLAN information to all the switches in a VTP domain.
C. The Dynamic Host Configuration Protocol (DHCP) is a standardized network protocol used on Internet Protocol (IP) networks for dynamically distributing network configuration parameters, such as IP addresses for interfaces and services.
References:
Stewart, James Michael, CompTIA Security+ Review Guide, Sybex, Indianapolis, 2014, p. 24
http://en.wikipedia.org/wiki/VLAN_Trunking_Protocol
http://en.wikipedia.org/wiki/Dynamic_Host_Configuration_Protocol
http://en.wikipedia.org/wiki/Virtual_LAN
NEW QUESTION: 3
SysOps管理者は、セキュリティのベストプラクティスがAWSアカウントのrootユーザーで実行されていることを確認する必要があります。
これが行われたことを管理者はどのように確認する必要がありますか?
A. ルートユーザーの構成を管理するAWS ArtifactからAWSコンプライアンスドキュメントを定期的に配布します。
B. AWS CLIを定期的に使用して、rootユーザーのパスワードを変更します。
C. AWS CLIを定期的に使用して、rootユーザーのアクセスキーとシークレットキーをローテーションします。
D. AWS Trusted Advisorのセキュリティチェックを使用して、ルートユーザーの構成を確認します。
Answer: D
Also when enabling AAA:
R1#sh run | sec aaa
aaa new-model
aaa authentication login default local
aaa session-id common
NEW QUESTION: 2
An administrator needs to connect a router in one building to a router in another using Ethernet. Each router is connected to a managed switch and the switches are connected to each other via a fiber line. Which of the following should be configured to prevent unauthorized devices from connecting to the network?
A. Configure only one of the routers to run DHCP services
B. Implement port security on the switches
C. Configure each port on the switches to use the same VLAN other than the default one
D. Enable VTP on both switches and set to the same domain
Answer: B
Explanation:
Port security in IT can mean several things:
The physical control of all connection points, such as RJ-45 wall jacks or device ports, so that no unauthorized users or unauthorized devices can attempt to connect into an open port.
The management of TCP and User Datagram Protocol (UDP) ports. If a service is active and assigned to a port, then that port is open. All the other 65,535 ports (of TCP or UDP) are closed if a service isn't actively using them.
Port knocking is a security system in which all ports on a system appear closed. However, if the client sends packets to a specific set of ports in a certain order, a bit like a secret knock, then the desired service port becomes open and allows the client software to connect to the service.
Incorrect Answers:
A. A basic switch not configured for VLANs has VLAN functionality disabled or permanently enabled with a default
VLAN that contains all ports on the device as members. Every device connected to one of its ports can send packets to any of the others. Separating ports by VLAN groups separates their traffic very much like connecting the devices to another, distinct switch of their own. Configuration of the first custom VLAN port group usually involves removing ports from the default VLAN, such that the first custom group of VLAN ports is actually the second VLAN on the device, in addition to the default VLAN
B. VLAN Trunking Protocol (VTP) is a Cisco proprietary protocol that broadcasts the definition of Virtual Local Area
Networks (VLAN) on the whole local area network. VTP achieves this by carrying VLAN information to all the switches in a VTP domain.
C. The Dynamic Host Configuration Protocol (DHCP) is a standardized network protocol used on Internet Protocol (IP) networks for dynamically distributing network configuration parameters, such as IP addresses for interfaces and services.
References:
Stewart, James Michael, CompTIA Security+ Review Guide, Sybex, Indianapolis, 2014, p. 24
http://en.wikipedia.org/wiki/VLAN_Trunking_Protocol
http://en.wikipedia.org/wiki/Dynamic_Host_Configuration_Protocol
http://en.wikipedia.org/wiki/Virtual_LAN
NEW QUESTION: 3
SysOps管理者は、セキュリティのベストプラクティスがAWSアカウントのrootユーザーで実行されていることを確認する必要があります。
これが行われたことを管理者はどのように確認する必要がありますか?
A. ルートユーザーの構成を管理するAWS ArtifactからAWSコンプライアンスドキュメントを定期的に配布します。
B. AWS CLIを定期的に使用して、rootユーザーのパスワードを変更します。
C. AWS CLIを定期的に使用して、rootユーザーのアクセスキーとシークレットキーをローテーションします。
D. AWS Trusted Advisorのセキュリティチェックを使用して、ルートユーザーの構成を確認します。
Answer: D